Auto IPSec tunneling provides a secure tunnel between two networked peer controllers or service platforms and associated access points which are within a range of valid IP addresses. Administrators can define which packets are sent within the tunnel, and how they‘re protected. When a tunnelled peer sees a sensitive packet, it creates a secure tunnel and sends the packet through the tunnel to its remote peer destination or associated access point
Tunnels are sets of security associations (SA) between two peers. SAs define the protocols and algorithms applied to sensitive packets and specify the keying mechanisms used by tunnelled peers. SAs are unidirectional and exist in both the inbound and outbound direction. SAs are established per the rules and conditions of defined security protocols (AH or ESP).
Internet Key Exchange (IKE) protocol is a key management protocol standard used in conjunction with IPSec. IKE enhances IPSec by providing additional features, flexibility, and configuration simplicity for the IPSec standard. IKE enables secure communications without time consuming manual pre-configuration for auto IPSec tunneling.
To define an Auto IPSec Tunnel configuration or override that can be applied to a profile:
Select the Configuration tab from the Web U.
Select Profiles from the Configuration tab.
Select Manage Profiles from the Configuration > Profiles menu.
Select Security.
Select Auto IPSec Tunnel.
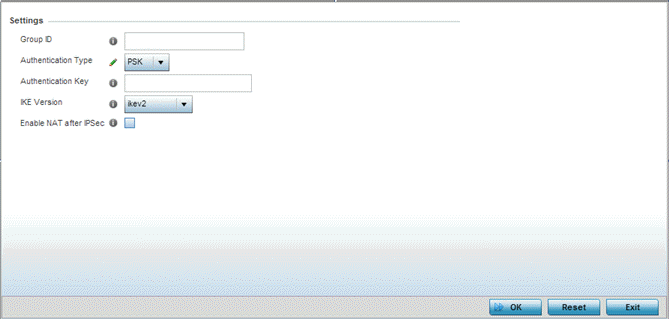
The Settings field lists those Auto IPSec tunnel policies created thus far. Any of these policies can be selected and applied to a profile
|
Group ID |
Define a 1 - 64 character identifier for an IKE exchange supporting auto IPSec tunnel secure peers. |
|
Authentication Type |
Use the drop-down menu to select either RSA or PSK (Pre Shared Key) as the authentication type for secure peer authentication on the auto IPSec secure tunnel. Rivest, Shamir, and Adleman (RSA) is an algorithm for public key cryptography. It‘s the first algorithm known to be suitable for signing, as well as encryption. The default setting is RSA |
|
Authentication Key |
Enter the 8 - 21 character shared key (password) used for auto IPSec tunnel secure peer authentication. |
|
IKE Version |
Use the drop-down menu to select the IKE version used for auto IPSec tunnel secure authentication with the IPSec gateway. |
|
Enable NAT after IPSec |
Select this option to enable internal source port NAT on the auto IPSec secure tunnel. |
|
Use Unique ID |
Select this option to use a unique ID with auto IPSec secure authentication for the IPSec remote gateway (appending the MiNT ID). This setting is disabled by default. |
Select OK to save the changes made to the auto IPSec tunnel configuration. Select Reset to revert to the last saved configuration.