Home > User Interface > Configuration > Policy Configuration > Connection Profiles

 |
Menu path: Configuration > Policies and Access Control >Connection Profiles .
Connection profiles tie access point SSIDs together with Authentication Sourcesthe captive portal to be used, filters and provisioning. The listing of connection profiles includes two unique items:
 ), or enabled (
), or enabled ( ) or Disabled (
) or Disabled ( ).
). button used to preview CWP contents.
button used to preview CWP contents.Three tabs are used in definition connection profiles:
The  button can be used to preview the CWP that users will see for this
connection profile.
button can be used to preview the CWP that users will see for this
connection profile.
The fields on the setting page are:
| Field | Usage | Example |
|---|---|---|
| Profile Name | The name of the profile. The name can only use alphanumeric characters, dashes, period, and underscores. | Guest_registration |
| Profile Description | An optional description of the profile. | Used for visitors |
| Enable Profile | This option is only visible when a new profile is created. Indicates whether the connection profile is to be used or not. |

|
| Root Portal Module | The root of the CWP display. Portal modules are listed and defined in Configuration>Advanced Access Configuration>Portal Modules (Portal Modules). | Default portal policy |
| Active Preregistration |
This activates preregistration on the connection profile. Instead of applying access control to the currently connected device, a local account created during preregistration is used. Note that this disables the on-site registration for this connection profile. The authentication sources on the connection profile must have Create local account enabled. |

|
| Automatically Register Clients | This activates automatic registration of clients for the profile. If 802.1X authentication is used clients will not be shown a captive portal and RADIUS authentication credentials will be used to register the device. If the type of connection is MAC authentication, the authentication source will be used to compute a role and access duration. |

|
| Reuse 802.1X Credentials |
This option emulates single sign-on (SSO) when the captive portal is presented after a successful 802.1X connection. The 802.1X credentials are reused on the portal to match an authentication. As a security precaution, this option will only reuse 802.1X credentials if there is an authentication source matching the provided realm. For example, if a user presents 802.1X credentials with a domain part (username@domain or domain\username), the domain part needs to be configured as a realm and an authentication source needs to be configured for that realm. If a domain component is not used in the 802.1X credentials, only the null realm will be match if an authentication source is configured for it. |
|
| 802.1X Recompute Role from Portal | If enabled, A3 will not use the role initially computed on the portal, but will instead use the dot1x username to recompute the role. |
|
| 802.1x Unset on Unmatch | If enabled, the role of the device will be unset if no authentication source returns a role. |

|
| Enable DPSK | This enables the Dynamic Pre-shared Key (DPSK) feature on this connection profile. The RADIUS server will provide the PSK key to use to connect on an SSID. |
|
| Default PSK Key | The default PSK when Enable DPSK is set. | |
| Automatically Deregister Clients on Accounting Stop | If set, A3 will deregister a device if it receives an RADIUS accounting stop message. |
|
| VLAN Pool Technique | The algorithm used to calculate the VLAN in a VLAN pool. One of username_hash or round_robin. | username_hash |
| Filters | See the Filters section below. | |
| Filter | ||
| Advanced Filter | ||
| Sources | Authentication sources are added to the connection
profile. Select a source from the drop-down list for the first
source. Add others using the  sign next to an existing source. Sources are evaluated in
order; they can be moved by hovering over a source number and moving
the symbol that displays up to the correct position. sign next to an existing source. Sources are evaluated in
order; they can be moved by hovering over a source number and moving
the symbol that displays up to the correct position. |
sms, email, sponsor, null |
| Billing Tiers | Specific billing tiers to be used with Billing Authentication Sources | |
| Provisioners | Provisioners to be used upon successful authentication. | |
| Scanners | Conformance scanners to be used before completing authentication. | |
| Device registration | Self Service Portal setting that can restrict role based on operating system. |
Filters
Connection profile filters restrict the application of a profile to specific network and device values. There are three fields related to filters:
Filter List
The possible filter items are:
| Filter Name | Options | Example | |
|---|---|---|---|
| Connection Sub Type |
|
|
EAP-FAST |
| Connection Type |
|
|
Wireless-802.11-EAP |
| Network | A network in CIDR format or an IP address | 192.168.1.0/24 | |
| Client Role | One of the defines Roles. | guest | |
| Port | A switch port number of the format <SwitchID>-<port> | ||
| Realm | One of the defined realms in Domains and Realms. | LOCAL | |
| SSID | The name of an access point SSID. As you enter characters into this field, a search will begin over defined SSIDs. A new one can be defined at that time. | Company-Guests | |
| Device | One of the defined Network Devices . | Corp AP | |
| Device Group | One of the defined device groups in Network Devices . | Extreme Networks APs | |
| Device MAC Address | A device's MAC address. | 11:22:33:44:55:66 | |
| Device Port | The device's port number. | 4 | |
| Tenant | The tenant's number | 2 | |
| Time Period |
The current time is within a time period expressed as described here. For example, working hours can be expressed as wd {Mon-Fri} hr {9am-5pm}. |
wd {Mon-Fri} hr {9am-5pm} | |
| URL | The URL of the captive portal path used by the client. | http://a3.example.com/register#bob | |
| FQDN | The FQDN of the captive portal path used by the client. | a3-external.example.com | |
| VLAN | VLAN during authentication. | 10 | |
Advanced Filter
An expression involving terms separated by the following operators:
The following attributes are available to use in advanced filters:
| Database Attributes from a Previous Connection | Attributes from the Current Connection |
|---|---|
|
|
For example,
The theory behind CWP modules is described in Captive Web Portal. The fields in the captive portal page are:
| Field | Usage | Example |
|---|---|---|
| Logo | The file used for the logo displayed at the top of
the CWP page. A new logo page can be uploaded using the  button. The location of the file is shown in this field
when the upload is completed. button. The location of the file is shown in this field
when the upload is completed. |
/common/logo.vertical.fullColor |
| Redirection URL | The default URL to redirect to on completion of registration. This is overridden by a per-security event redirect URL. | https://www.extremenetworks.com |
| Force Redirection URL | If enabled, the user is redirect to the Redirection URL defined above. If disable, the user is allowed to access their originally intended page. |

|
| Block Interval | The number of times that a user can retry a login, SMS, or SMS PIN request is defined below. Block Interval indicates how long a user will have to wait until attempting to reauthenticate after having exceeded any of the limits. Expressed as a number of time units from seconds to years. | 10 minutes |
| SMS PIN Retry Limit | The maximum number of times a user can retry a SMS PIN before having to request another PIN. A value of 0 disables the limit. | 0 |
| SMS Request Retry Limit | The maximum number of times a user can request a SMS PIN. A value of 0 disables the limit. | 0 |
| Login Attempt Limit | Limit the number of login attempts. A value of 0 disables the limit. | 0 |
| Allow access to Registration Portal when Registered | This enables already registered users to be able to re-register their device by first accessing the status page and then accessing the portal. This is useful to allow users to extend their access even though they are already registered and to manage which devices are registered within their limits. Billing options use this option. |

|
| Network Logout | If enabled, users can access the network logout page (http://undefined/networklogoff) in order to terminate their network access and switch their device back to unregistered. |

|
| Network Logout Popup | If Network Logout is enabled and this option is enabled, a log off popup will be presented at the end of the registration process. |

|
| Languages | Enables a list of languages that the user can choose from during authentication. | en_US |
The files tab lists all of the pages associated with the connection profile and CWP. Each connection profile includes its own copy of files. Editing one profile's files will not affect any other profile.
Folders can be expanded and collapsed by selecting them.
Pages are edited by selecting the page in the list. Pages can be viewed, copied, or reverted using the three icons to the right of the list.
The follow pages are most often customized:
The editor provides the following controls:
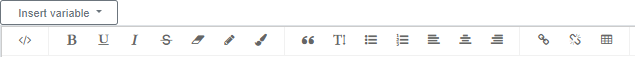
| Control | Usage |
|---|---|
| Insert variable | At run-time will insert the value of a variable. The variable
choices are:
|
| </> | Toggles between a simple text display and a display of the underlying HTML source. |
B
U
I
 |
Character effects: bold, underline, italics, and strikethrough. |
 |
Removes a color effect from the current text selection. |
 |
Sets the text color for the current selection. |
 |
Sets the background text color for the current selection. |
 |
Places the selected paragraph into a highlighted box. |
 |
Changes the font size of the selected text. No visibile indication is shown in the editor. |
 |
Creates or removes an unordered (bulleted) list for the selected lines. |
 |
Creates or removes an ordered (numbered) list for the selected lines. |
 |
Sets the alignment for the selected text to left, center, or right respectively. |
 |
Creates or deletes a link to an external file. The following
parameters are required to create a link:
|
 |
Inserts a table of a selected size. |
Copyright © 2023 Extreme Networks. All rights reserved. Published March 28, 2023.