XCO User Authentication and Authorization
XCO users are validated with Unix authentication or LDAP and managed with Role-based Access Control (RBAC).
At installation time, starting with EFA 2.5.0, all XCO users of services such as MySQL and RabbitMQ are assigned random passwords that are stored in XCO configuration files. This satisfies the requirement to enforce the change of default passwords, and no two XCO installations share identical passwords.
For more information, see XCO RBAC Policy Enforcement and Assign and View XCO Roles.
Authentication
- Unix authentication (local and remote) on the host where XCO is installed. Host credentials are the default validation method if LDAP validation fails.
- External LDAP server: Users configured in LDAP use their LDAP credentials to log in to XCO.
- Authentication support:
- Unix authentication
- Local users - Users created in XCO and stored in the database
- External
authentication
- LDAP
- TACACS
- Auth preference and fallback
The following graphic illustrates how users can check all modes of authtication at the same time. Define the authentication preference to help users to configure multiple modes of authentication at once.
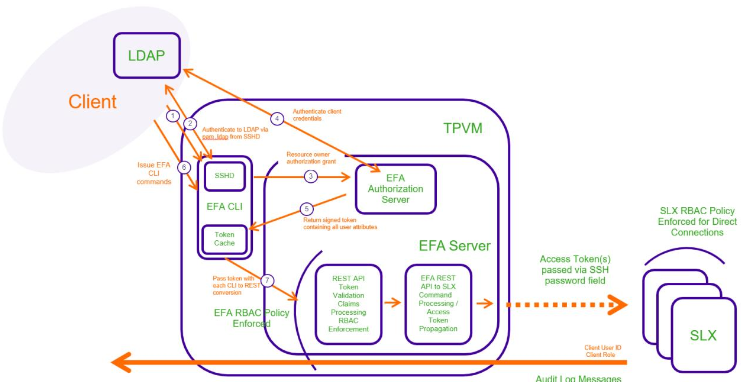
Operational or maintenance tasks are propagated to SLX devices through OAuth2 and JWT access tokens. TLS is used for connections with SLX devices. The OpenStack ML2 plugin also uses TLS and OAuth2 tokens. When XCO is installed in secure mode, traffic to northbound interfaces uses TLS. For more information about secure mode, see the "XCO Installation Modes" topic in the ExtremeCloud Orchestrator Deployment Guide, 3.2.0 .
Authentication Policy CLI configuration
For CLI users, the auth preference configuration is available under efa auth authentication preference.
KVM:~$ efa auth authentication preference Available Commands: add Add the authentication preference update Update the authentication preference delete Delete the authentication preference show show authentication preference
Show authentication preference:
KVM:~$ efa auth authentication preference show +-----------+------------+------------+ | Auth Type | Identifier | Preference | +-----------+------------+------------+ | HOST | HOST | 1 | +-----------+------------+------------+
Add authentication preference:
KVM:~$ efa auth authentication preference add --authType=LOCAL --identifier=LOCAL --preference=3 Successfully updated the auth preference. +-----------+------------+------------+ | Auth Type | Identifier | Preference | +-----------+------------+------------+ | LOCAL | LOCAL | 3 | +-----------+------------+------------+
Show authentication preference:
KVM:~$ efa auth authentication preference show +-----------+------------+------------+ | Auth Type | Identifier | Preference | +-----------+------------+------------+ | HOST | HOST | 1 | +-----------+------------+------------+ | LOCAL | LOCAL | 3 | +-----------+------------+------------+
Update authentication preference:
KVM:~$ efa auth authentication preference update --authType=LOCAL --identifier=LOCAL --preference=2 Successfully updated the auth preference. +-----------+------------+------------+ | Auth Type | Identifier | Preference | +-----------+------------+------------+ | LOCAL | LOCAL | 2 | +-----------+------------+------------+ KVM:~$ efa auth authentication preference delete --authType=LOCAL --identifier=LOCAL
Add authentication preference for TACACS authentication:
efa auth authentication preference add --authType=TACACS --identifier=10.37.135.12 --preference=3 Successfully added the auth preference. +-----------+--------------+------------+ | Auth Type | Identifier | Preference | +-----------+--------------+------------+ | TACACS | 10.37.135.12 | 3 | +-----------+--------------+------------+ efa auth authentication preference add --authType=LDAP --identifier=kvm12.com --preference=4 Successfully added the auth preference.
Add authentication preference for LDAP authentication:
efa auth authentication preference add --authType=LDAP --identifier=kvm12.com --preference=4 Successfully added the auth preference. +-----------+------------+------------+ | Auth Type | Identifier | Preference | +-----------+------------+------------+ | LDAP | kvm12.com | 4 | +-----------+------------+------------+
Show authentication preference:
efa auth authentication preference show +-----------+--------------+------------+ | Auth Type | Identifier | Preference | +-----------+--------------+------------+ | HOST | HOST | 1 | +-----------+--------------+------------+ | LOCAL | LOCAL | 2 | +-----------+--------------+------------+ | TACACS | 10.37.135.12 | 3 | +-----------+--------------+------------+ | LDAP | kvm12.com | 4 | +-----------+--------------+------------+
Authorization
After XCO is deployed, the installer has the role of SystemAdmin and has complete access to XCO functionality. For installation on TPVM, this user has the user name ‘extreme‘. By default, no other host OS users can access XCO unless the SystemAdmin assigns the appropriate roles. RBAC occurs on XCO and API.

