You can add specific policy rules at the interface level in addition to the built-in rules. Such rules give you the capability of restricting access to a port, for specific reasons, such as a Denial of Service (DoS) attack.
The policy rules are set up in the same manner as policy rules defined for a Role — specify an IP address, select a protocol if applicable, and then either allow or deny traffic to that address. For more information, see Policy Rules.
The rules defined for port exception filters are prepended to the normal set of restrictive exception filters and have precedence over the system's normal protection enforcement (that is, they are evaluated first).

Warning
If defined improperly, user exception rules may seriously compromise the system‘s normal security enforcement rules. They may also disrupt the system's normal operation and even prevent system functionality altogether. It is advised to only augment the exception-filtering mechanism if absolutely necessary.To Define Interface Exception Filters:
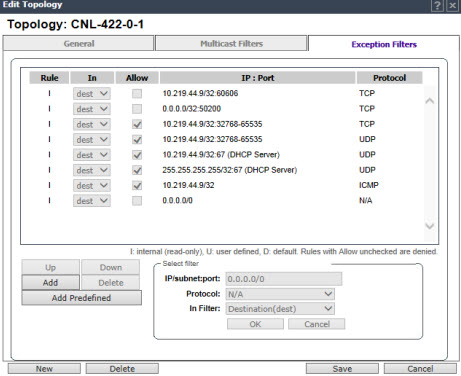
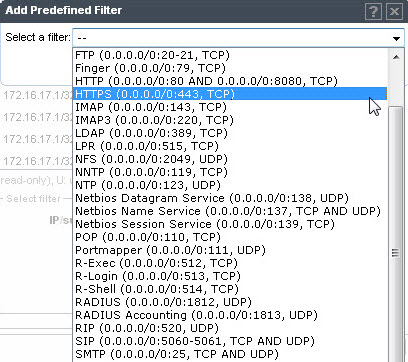
In the IP / subnet:port box, type the destination IP address. You can also specify an IP range, a port designation, or a port range on that IP address.
In the Protocol drop-down list, click the protocol you want to specify for the filter. This list may include UDP, TCP, GRE, IPsec-ESP, IPsec-AH, ICMP (Internet Control Message Protocol). The default is N/A.

 Print
this page
Print
this page Email this topic
Email this topic Feedback
Feedback