Addinting Editing Crypto Map
About this task
You can add a new crypto map or edit an existing crypto map.
Procedure
- If requiring a new crypto map configuration, select the Add button. If updating the configuration of an existing crypto map, select it from amongst those available and select the Edit button.
-
If adding a new crypto map,
assign it a name up to 32 characters as a unique identifier. Select the
Continue button to proceed to the VPN Crypto Map
screen.
 Profile Security - VPN Crypto Map Entry Screen
Profile Security - VPN Crypto Map Entry Screen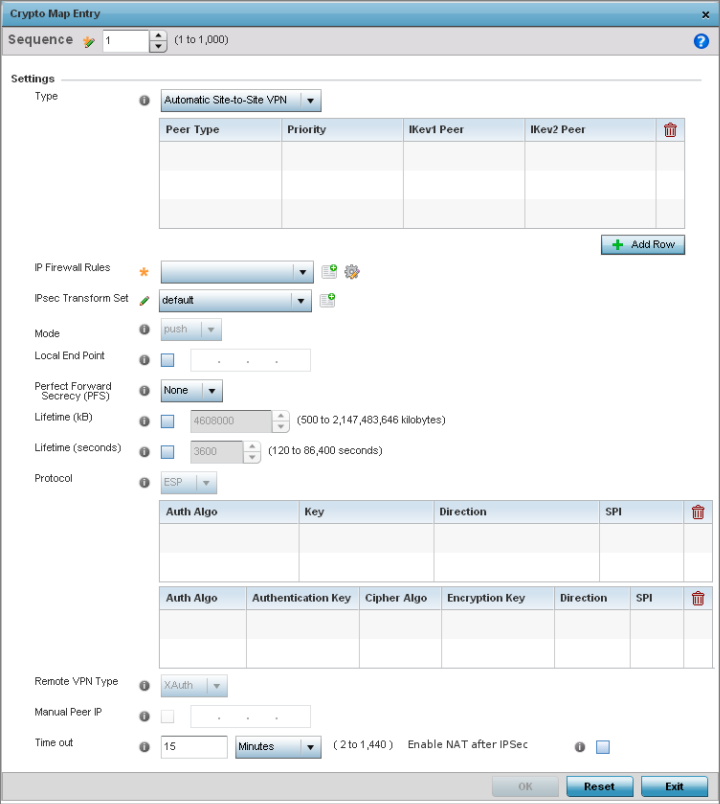
-
Define the following parameters
to set the crypto map configuration:
Sequence
Each crypto map configuration uses a list of entries based on a sequence number. Specifying multiple sequence numbers within the same crypto map extends connection flexibility to multiple peers on the same interface, based on this selected sequence number (from 1 - 1,000).
Type
Define the site-to-site-manual, site-to-site-auto or remote VPN configuration defined for each listed crypto map configuration.
IP Firewall Rules
Use the drop-down menu to select the ACL used to protect IPSec VPN traffic. New access/deny rules can be defined for the crypto map by selecting the Create icon, or an existing set of firewall rules can be modified by selecting the Edit icon.
IPSec Transform Set
Select the transform set (encryption and hash algorithms) to apply to this crypto map configuration.
Mode
Use the drop-down menu to define which mode (pull or push) is used to assign a virtual IP. This setting is relevant for IKEv1 only, since IKEv2 always uses the configuration payload in pull mode. The default setting is push.
Local End Point
Select this option to define an IP address as a local tunnel end-point address. This setting represents an alternative to an interface IP address.
Perfect Forward Secrecy (PFS)
PFS is key-establishment protocol, used to secure VPN communications. If one encryption key is compromised, only data encrypted by that specific key is compromised. For PFS to exist, the key used to protect data transmissions must not be used to derive any additional keys. Options include None, 2, 5 and 14. The default setting is None.
Lifetime (KB)
Select this option to define a connection volume lifetime (in kilobytes) for the duration of an IPSec VPN security association. Once the set volume is exceeded, the association is timed out. Use the spinner control to set the volume from 500 - 2,147,483,646 kilobytes.
Lifetime (seconds)
Select this option to define a lifetime (in seconds) for the duration of an IPSec VPN security association. Once the set value is exceeded, the association is timed out. The available range is from 120 - 86,400 seconds. The default setting is 120 seconds.
Protocol
Select the security protocol used with the VPN IPSec tunnel connection. SAs are unidirectional, existing in each direction and established per security protocol. Options include ESP and AH. The default setting is ESP.
Remote VPN Type
Define the remote VPN type as either None or XAuth. XAuth (extended authentication) provides additional authentication validation by permitting an edge device to request extended authentication information from an IPSec host. This forces the host to respond with additional authentication credentials. The edge device respond with a failed or passed message. The default setting is XAuth.
Manual Peer IP
Select this option to define the IP address of an additional encryption/ decryption peer.
Time Out
Select this option to set the IPSec SA time out value. Use the textbox and the drop-down list to configure the time out duration.
Enable NAT after IPSec
Select this option to enable NAT after IPSec. Enable this if there are NATted networks behind VPN tunnels.
-
Select OK to save the
updates made to the Crypto Map Entry screen.
Selecting Reset reverts the screen to its last saved setting.


