Transform Set Configuration
A transform set is a combination of security protocols, algorithms and other settings applied to IPSec protected traffic. One crypto map is utilized for each IPsec peer, however for remote VPN deployments one crypto map is used for all the remote IPsec peers.
-
Select the Transform Set
tab.
Create or modify transform set configurations to specify how traffic is protected.
 Profile Security - VPN Transform Set Screen
Profile Security - VPN Transform Set Screen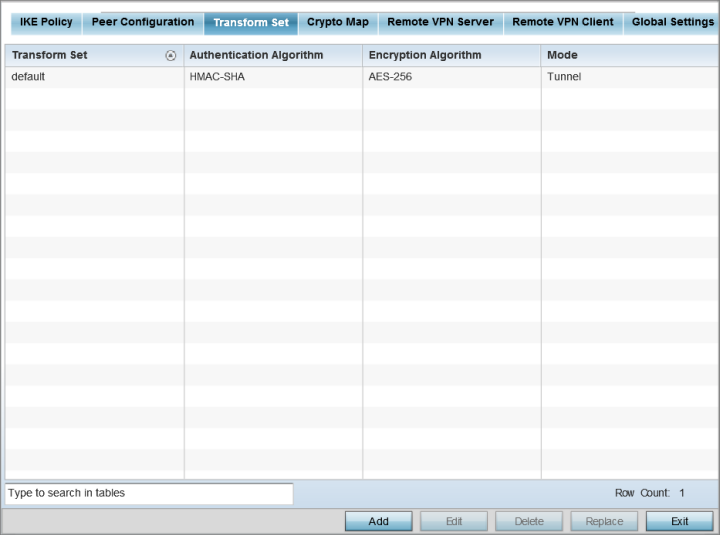
-
Review the following attributes
of existing Transform Set configurations:
Name
The 32-character maximum name assigned to each listed transform set upon creation. A transform set is a combination of security protocols, algorithms, and other settings applied to IPSec protected traffic.
Authentication Algorithm
Lists each transform sets‘s authentication scheme used to validate identity credentials. The authentication scheme is either HMAC-SHA or HMAC-MD5.
Encryption Algorithm
Displays each transform set‘s encryption method for protecting transmitted traffic.
Mode
Displays either Tunnel or Transport as the IPSec tunnel type used with the transform set. Tunnel is used for site-to-site VPN and Transport should be used for remote VPN deployments.
