Access Control Lists
|
Feature |
Product |
Release introduced |
|---|---|---|
|
Access Control List (ACL)-based filtering, including egress ACLs, ingress ACLs, Layer 2 to Layer 4 filtering, port-based, and VLAN-based |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.4 |
|
|
5520 Series |
VOSS 8.2.5 |
|
|
5720 Series |
Fabric Engine 8.7 |
|
|
7520 Series |
Fabric Engine 8.10 |
|
|
7720 Series |
Fabric Engine 8.10 |
|
|
VSP 4450 Series |
VSP 4000 4.0 |
|
|
VSP 4900 Series |
VOSS 8.1 |
|
|
VSP 7200 Series |
VOSS 4.2.1 |
|
|
VSP 7400 Series |
VOSS 8.0 |
|
|
VSP 8200 Series |
VSP 8200 4.0 |
|
|
VSP 8400 Series |
VOSS 4.2 |
|
|
VSP 8600 Series |
VSP 8600 4.5 |
|
|
XA1400 Series |
VOSS 8.0.50 |
|
|
InVSN Filter |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.4 |
|
|
5520 Series |
VOSS 8.2.5 |
|
|
7520 Series |
Fabric Engine 8.10 |
|
|
7720 Series |
Fabric Engine 8.10 |
|
|
5720 Series |
Fabric Engine 8.7 |
|
|
VSP 4450 Series |
VOSS 7.0 |
|
|
VSP 4900 Series |
VOSS 8.1 |
|
|
VSP 7200 Series |
VOSS 7.0 |
|
|
VSP 7400 Series |
VOSS 8.0 |
|
|
VSP 8200 Series |
VOSS 7.0 |
|
|
VSP 8400 Series |
VOSS 7.0 |
|
|
VSP 8600 Series |
Not Supported |
|
|
XA1400 Series |
Not Supported |
|
|
IPv6 ingress filters |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.4 |
|
|
5520 Series |
VOSS 8.2.5 |
|
|
5720 Series |
Fabric Engine 8.7 |
|
|
7520 Series |
Fabric Engine 8.10 |
|
|
7720 Series |
Fabric Engine 8.10 |
|
|
VSP 4450 Series |
VOSS 4.1 |
|
|
VSP 4900 Series |
VOSS 8.1 |
|
|
VSP 7200 Series |
VOSS 4.2.1 |
|
|
VSP 7400 Series |
VOSS 8.0 |
|
|
VSP 8200 Series |
VOSS 4.1 |
|
|
VSP 8400 Series |
VOSS 4.2 |
|
|
VSP 8600 Series |
VSP 8600 6.2 |
|
|
XA1400 Series |
Not Supported |
|
|
IPv6 egress filters |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.4 |
|
|
5520 Series |
VOSS 8.2.5 |
|
|
5720 Series |
Fabric Engine 8.7 |
|
|
7520 Series |
Fabric Engine 8.10 |
|
|
7720 Series |
Fabric Engine 8.10 |
|
|
VSP 4450 Series |
VOSS 7.0 |
|
|
VSP 4900 Series |
VOSS 8.1 |
|
|
VSP 7200 Series |
VOSS 7.0 |
|
|
VSP 7400 Series |
VOSS 8.0 |
|
|
VSP 8200 Series |
VOSS 7.0 |
|
|
VSP 8400 Series |
VOSS 7.0 |
|
|
VSP 8600 Series |
Not Supported |
|
|
XA1400 Series |
Not Supported |
|
|
IPv6 ACL DSCP Remarking |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.5 |
|
|
5520 Series |
VOSS 8.5 |
|
|
5720 Series |
Fabric Engine 8.7 |
|
|
7520 Series |
Fabric Engine 8.10 |
|
|
7720 Series |
Fabric Engine 8.10 |
|
|
VSP 4450 Series |
Not Supported |
|
|
VSP 4900 Series |
VOSS 8.5 |
|
|
VSP 7200 Series |
Not Supported |
|
|
VSP 7400 Series |
VOSS 8.5 |
|
|
VSP 8200 Series |
Not Supported |
|
|
VSP 8400 Series |
VOSS 8.5 Switch model: VSP 8404C |
|
|
VSP 8600 Series |
Not Supported |
|
|
XA1400 Series |
Not Supported |
Apply rules to incoming and outgoing traffic. The total number of ACLs that you can configure differs depending on the switch.
An ACL can filter either IPv6 or non-IPv6 packets. By default, an ACL filters non-IPv6 packets. You must specify the packet type as IPv6 at the ACL level to enable IPv6 filtering. You cannot change the packet type for the ACL after you configure it. If you need a different packet type, you must delete the ACL, and then re-create it with the other packet type.
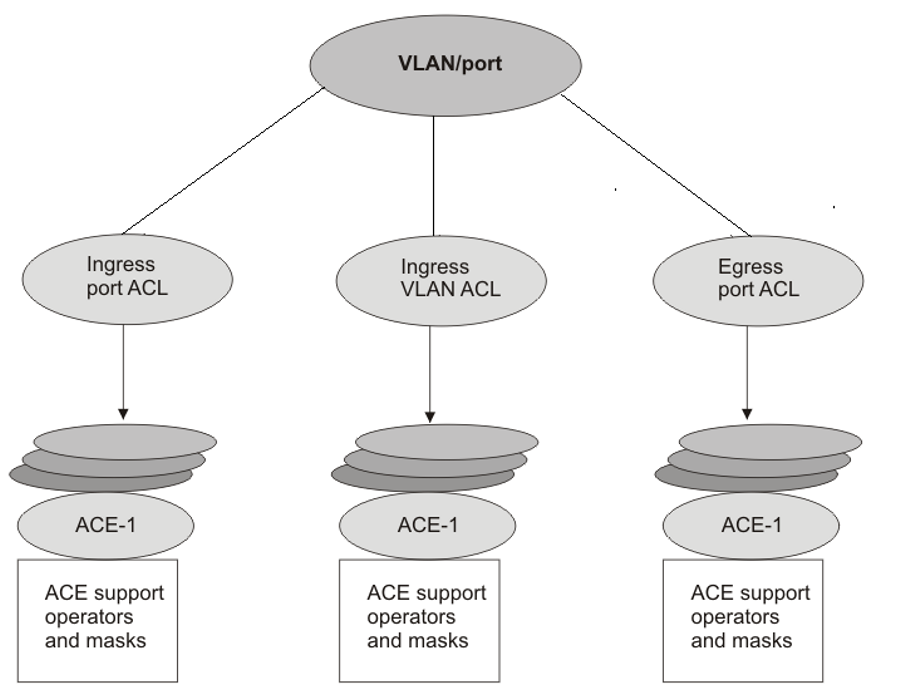
You can associate an ACL with the following interfaces:
-
Ingress port (inPort)
-
Ingress VLAN (inVLAN)
-
Ingress VSN (inVSN)
-
Egress port (outPort)
Note
VLAN-based ACL filters are not supported on a DvR Leaf node.
Note
All ACLs are enabled when a DvR Leaf node is created. When creating the DvR Leaf node, or when you enable IS-IS globally, the message dvr leaf [x] displays in CLI. If the DvR Leaf node is reset or reconnects to the DvR domain, this message does not display but the same principle applies. As a best practice, delete ACLs not used on DvR Leaf nodes, rather than disable them, because the ACLs re-enable without warning after a DvR domain transition caused by reset, or protocol or link bounce.
The ingress VLAN ACL associations apply to all active port members of a VLAN. An ACL is created in the enabled state by default.
The InVSN Filter is an Access Control List (ACL) that can be used with MAC-in-MAC (MIM) encapsulated packets that are received on the NNI ingress ports and are routed or bridged to UNI ports or terminated on the fabric node. The InVSN Filter matches and filters IPv4 and IPv6 packet headers coming on UNI ports only, NNI ports only, or both UNI and NNI ports. The InVSN Filter does not filter packets that arrive on NNI ingress ports but are bridged to other NNI ports or are for transit traffic.
An ACL can contain multiple filter rules called Access Control Entries (ACE). ACEs provide match criteria and rules for ACL-based filters. An ACE can provide actions such as dropping a packet, monitoring a packet, or remarking QoS on a packet. Complete lists of actions are provided in the Access Control Entries section. After an ingress or egress packet meets the match criteria specified in ACEs within an ACL, the system executes the predefined action.
ACLs provide the ability to configure default and global actions. A default action is applied when no filter rule (ACE) matches on a packet flow. The global action is executed when any filter rule (ACE) matches on a packet flow. The default action mode for ACLs is permit. ACL global actions are:
-
monitor-dst-mlt
-
monitor-dst-ports
The following figure shows the relationships between ACEs and VLAN- and port-based ACLs.