Profile Overrides - Auto IPSec Tunnel
About this task
IPSec tunnels are established to secure traffic, data and management traffic, from access points to remote wireless controllers. Secure tunnels must be established between access points and the wireless controller with minimum configuration pushed through DHCP option settings.
To override profile's Auto IPSec Tunnel configuration:
Procedure
-
Go to Configuration →
Devices → Device Overrides.
The Device Overrides screen displays. This screen lists devices within the managed network.
-
Select an access point.
The selected access point's configuration menu displays.
-
Expand Profile Overrides
→ Security and select Auto IPSec
Tunnel.
The Auto IPSec Tunnel configuration screen displays.
 Profile Overrides - Security - Auto IPSec Tunnel Configuration Screen
Profile Overrides - Security - Auto IPSec Tunnel Configuration Screen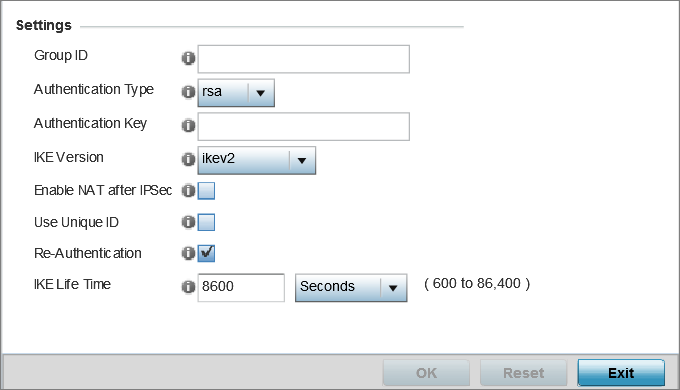
-
Refer to the following table to
configure the Auto IPSec Tunnel settings:
Group ID
Configure the ID string used for IKE authentication. String length can be between 1 and 64 characters.
Authentication Type
Set the IPSec Authentication Type. Options include PSK (Pre Shared Key) or RSA.
Authentication Key
Set the common key for authentication between the remote tunnel peer. Key length is between 8 and 21 characters.
IKE Version
Configure the IKE version to use. The available options are: ikev1-main, ikev1- aggr and ikev2.
Enable NAT after IPSec
Select this option to enable NAT after IPSec. Enable this if there are NATted networks behind VPN tunnels.
Use Unique ID
In scenarios having different access points behind different NAT boxes and routers have the same IP address, it is not possible to create a tunnel between the wireless controller and the access point because the wireless controller does not identify the access point uniquely. When this option is selected, each access point behind a same NAT box or router will have an unique ID which is used to create the VPN tunnel.
Re-Authentication
Select this option to re-authenticate the key on a IKE rekey. This setting is disabled by default.
IKE Life Time
Set a lifetime in either seconds (600 - 86,400), minutes (10 - 1,440), hours (1 - 24), or days (1) for IKE security association duration. The default setting is 8600 seconds.
-
Click OK to save the
Auto IPSec Tunnel configuration changes.
Click Reset to revert to the last saved configuration.


