Private VLANs
|
Feature |
Product |
Release introduced |
|---|---|---|
|
E-Tree and Private VLANs |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.4 |
|
|
5520 Series |
VOSS 8.2.5 |
|
|
Routing on Private VLANs |
5320 Series |
Fabric Engine 8.6 |
|
5420 Series |
VOSS 8.5 |
|
|
5520 Series |
VOSS 8.5 |
Private VLANs provide isolation between ports within a Layer-2 service.
The primary and secondary VLAN make the private VLAN. Standard VLAN configuration takes place on the primary VLAN. The secondary VLAN is used to label traffic ingressing isolated ports.
Ports in the private VLAN are configured as isolated, promiscuous, or trunk. The default value is None.
Port Types
Note
Layer 2 and Layer 3 services based on port types also apply in any routing scenario between two private VLANs or E-trees.
|
Port type |
Description |
|---|---|
|
Promiscuous (tagged or untagged ports) |
Promiscuous ports communicate with all other ports within the private VLAN. Uses the primary VLAN. |
|
Isolated (tagged or untagged ports) |
Isolated ports communicate with the promiscuous ports, but not with any other isolated port. Uses the secondary VLAN. |
|
Trunk (tagged ports) |
Trunk ports carry traffic between other port members within the private VLANs. Accepts either primary or secondary VLAN. |
|
Port type |
Description |
|---|---|
|
Promiscuous (tagged or untagged ports) |
Promiscuous ports communicate with all other ports of any Layer 3 VLAN. |
|
Isolated (tagged or untagged ports) |
Isolated ports communicate with any promiscuous or regular VLAN ports but not with other isolated ports. |
|
Trunk (tagged ports) |
Trunk ports carry traffic between other port members within the private VLANs. |
Trunk ports must have VLAN encapsulation enabled. A port can be a single port or can belong to an MLT.
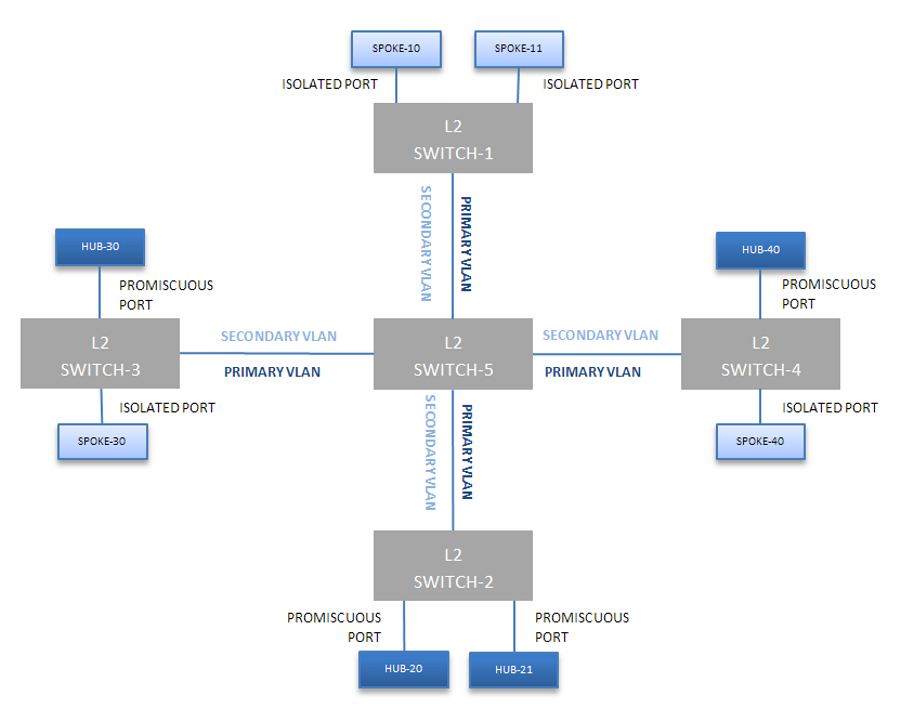
The following figure shows a basic private VLAN topology with private VLAN configured on five switches. All ports connecting to other switches are trunk type ports and all other ports are either promiscuous or isolated ports. On the secondary VLAN, spokes can communicate with hubs, and hubs can communicate with all spokes in the same private VLAN using the primary VLAN, however, spokes cannot communicate with other spokes.
E-Tree
The E-Tree allows private VLANs to traverse the Shortest Path Bridging MAC (SPBM) network.
For more information about E-Tree and SPBM configuration, see E-Tree and Private VLAN topology.
Routing on Private VLANs
You can route traffic out of a private VLAN (PVLAN) by applying an IP address to a PVLAN. IP routing is supported on private VLANs for edge switches. With PVLAN packet routing, two hosts located in different private VLANs can communicate over the network.
Packets can be routed over the network between the following:
-
regular VLAN and a private VLAN
-
different private VLANs
-
different I-SIDs (E-tree)
The number of private VLANs that you configure with an IP address influences the IPv4 Egress ACE count. For information about scaling information, see Fabric Engine Release Notes. Limits are not enforced; either number of private VLANs or number of private VLAN trunk ports can go beyond the recommended values. As a best practice, use the show io resources filter command to monitor allocated resources.
Note
You cannot enable IP Multicast on a private VLAN interface. ip spb-multicast enable and ip pim enable commands are not available on a private VLAN.
Private VLAN Configuration Rules
The following are private VLAN rules for the switch:
Use private VLANs for Layer 2 and Layer 3 services.
You cannot configure IP Source Guard (IPSG) on ports that are members of private VLANs.
Do not use the untag-port default vlan parameter on private VLAN interfaces that are operating as trunk ports, because it impacts the private VLAN functionality.

