Configuring RADIUS Server Policy
About this task
The RADIUS server ensures the information is correct using an authentication scheme like PAP, CHAP or EAP. The user's proof of identification is verified, along with, optionally, other information. A RADIUS server policy can also use an external LDAP resource to verify user credentials. The creation and utilization of a single RADIUS server policy is supported.
To manage the access point‘s RADIUS server policy:
Procedure
- Select Configuration → Services from the main menu.
-
Expand the RADIUS menu
option and select RADIUS Server.
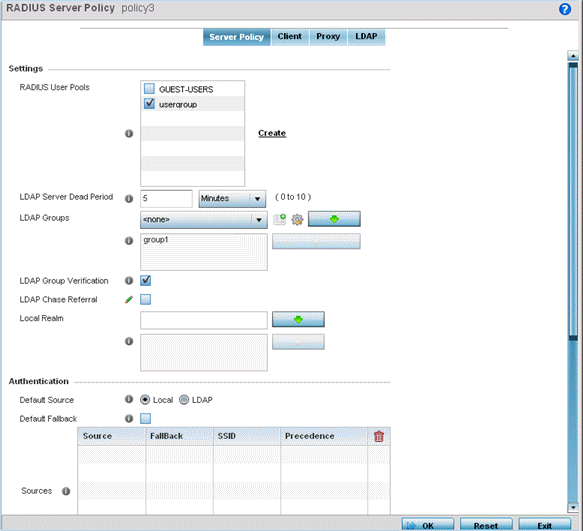
The RADIUS Server Policy screen displays with the Server Policy tab displayed by default.
 RADIUS Server Policy Screen - Server Policy Tab
RADIUS Server Policy Screen - Server Policy Tabs
-
Select Activate RADIUS Server
Policy to enable the parameters within the screen for
configuration.
Ensure that thiis option remains selected, or this RADIUS server configuration will not be applied to the access point profile.
-
Define the following settings required to create
or modify the server policy.
RADIUS Server Policy Select the user pools (groups of existing client users) to apply to this server policy. If there is not an existing user pool configuration suitable for the deployment, select the Create link and define a new configuration. For more information, see Defining User Pools. LDAP Server Dead Period Set an interval in either seconds (0 - 600) or minutes (0- 10) during which the access point will not contact its LDAP server resource. A dead period is only implemented when additional LDAP servers are configured and available. LDAP Groups Use the drop-down menu to select LDAP groups to apply the server policy configuration. Select the Create or Edit icons as needed to either create a new group or modify an existing group. Use the arrow icons to add and remove groups as required. LDAP Group Verification Select the check box to set the LDAP group search configuration. This setting is enabled by default. LDAP Chase Referral Select the check box to set the LDAP referral chase feature. This settings is enabled by default. When enabled, if the LDAP server does not contain the requested information, it indicates to the LDAP client that it does not have the requested information and provides the client with another LDAP server that could have the requested information. It is up to the client to contact the other LDAP server for its information. Local Realm Define the LDAP Realm performing authentication using information from an LDAP server. User information includes user name, password, and the groups to which the user belongs. -
Set the following Authentication parameters to
define server policy authorization settings.
Default Source Select the RADIUS resource for user authentication with this server policy. Options include Local for the local user database or LDAP for a remote LDAP resource. The default setting is Local. Default Fallback Select this option to indicate that fall back from RADIUS to local is enabled in case RADIUS authentication is not available for any reason. This option is enabled only when LDAP is selected as the Default Source. Use the Add Row button to add fallback sources into the Sources table. Provide the following information: - Source – Select the type of fallback. Select from LDAP or Local.
- Fallback – Select to enable fallback on this record.
- SSID – Enter the SSID to fall back on.
- Precedence – Use the spinner to select the precedence for selection of fallback.
Authentication Type Use the drop-down menu to select the EAP authentication scheme used with this policy. The following EAP authentication types are supported: - All – Enables both TTLS and PEAP
- TLS - Uses TLS as the EAP type
- TTLS and MD5 - The EAP type is TTLS with default authentication using MD5
- TTLS and PAP - The EAP type is TTLS with default authentication using PAP
- TTLS and MSCHAPv2 - The EAP type is TTLS with default authentication using MSCHAPv2
- PEAP and GTC - The EAP type is PEAP with default authentication using GTC
- PEAP and MSCHAPv2 - The EAP type
is PEAP with default authentication using MSCHAPv2
However, when user credentials are stored on an LDAP server, the RADIUS server cannot conduct PEAP-MSCHAPv2 authentication on its own, as it is not aware of the password. Use LDAP agent settings to locally authenticate the user. Additionally, an authentication utility (such as Samba) must be used to authenticate the user. Samba is an open source software used to share services between Windows and Linux machine.
Do Not Verify Username Enabled only when TLS is selected in Authentication Type. When selected, user name is not matched but the certificate expiry is checked. Enable CRL Validation Select this option to enable a Certificate Revocation List (CRL) check. Certificates can be checked and revoked for a number of reasons including failure or compromise of a device using a certificate, a compromise of a certificate key pair or errors within an issued certificate. This option is disabled by default. Enable EAP Termination Select this option to enable EAP Termination on the current RADIUS server policy. EAP Termination terminates EAP authentication at the controller Bypass CRL Check Select the option to bypass a certificate revocation list (CRL) check when a CRL is not detected. This setting is enabled by default. A CRL is a list of certificates that have been revoked or are no longer valid. Allow Expired CRL Select this option to allow the use of an expired CRL. This option is enabled by default 
Note
When you are using LDAP as authentication external source, the PEAP-MSCHAPV2 authentication type can be used only if the LDAP server returns the password as plain-text. PEAP-MSCHAPv2 authentication is not supported if the LDAP server returns encrypted passwords. This restriction does not apply for Microsoft's Active Directory Server. -
If you are using LDAP as the default
authentication source, select +
Add Row to set LDAP Agent settings.
When a user's credentials are stored on an external LDAP server, the controller or service platform‘s local RADIUS server cannot successfully conduct PEAP-MSCHAPv2 authentication, since it is not aware of the user‘s credentials maintained on the external LDAP server resource. Therefore, up to two LDAP agents can be provided locally so remote LDAP authentication can be successfully accomplished on the remote LDAP resource using credentials maintained locally.
Username Enter a 128-character maximum username for the LDAP server‘s domain administrator. This is the username defined on the LDAP server for RADIUS authentication requests. Password Enter and confirm the 32-character maximum password (for the username provided above). The successful verification of the password maintained on the controller or service platform enables PEAP-MSCHAPv2 authentication using the remote LDAP server resource. Retry Timeout Set the number of seconds (60 - 300) or minutes (1 - 5) to wait between LDAP server access requests when attempting to join the remote LDAP server‘s domain. The default setting is one minute. Redundancy Define the Primary or Secondary LDAP agent configuration used to connect to the LDAP server domain. Domain Name Enter the name of the domain (from 1 - 127 characters) to which the remote LDAP server resource belongs. -
Set the following Session Resumption/Fast
Reauthentication settings to define how server policy sessions
are re-established once terminated and require cached data to resume:
Enable Session Resumption Select the checkbox to control volume and the duration cached data is maintained by the server policy upon the termination of a server policy session. The availability and quick retrieval of the cached data speeds up session resumption. This setting is disabled by default. Cached Entry Lifetime If enabling session resumption, use the spinner control to set the lifetime (1 - 24 hours) cached data is maintained by the RADIUS server policy. The default setting is 1 hour. Maximum Cache Entries If enabling session resumption, use the spinner control to define the maximum number of entries maintained in cache for this RADIUS server policy. The default setting is 128 entries. -
Click OK to save the settings to
the server policy configuration.
Click Reset to revert to the last saved configuration.


