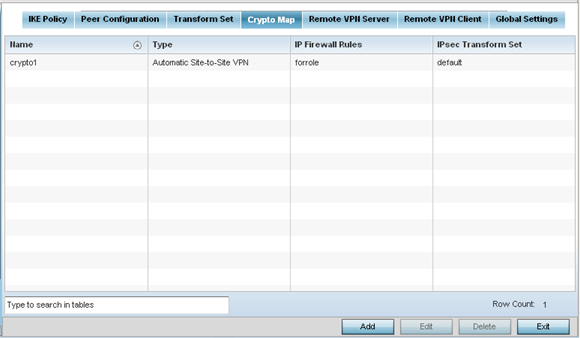
Crypto Map
Use crypto maps (as applied to IPSec VPN) to combine the elements used to create IPSec SAs (including transform sets).
To define a profile's VPN settings:
-
Select the Crypto Map tab.
-
Review the following Crypto Map configuration parameters to assess their relevance:
Name
Lists the 32 character maximum name assigned for each crypto map upon creation. This name cannot be modified as part of the edit process.
Type
Displays the site-to-site-manual, site-to-site-auto or remote VPN configuration defined for each listed cyrpto map configuration. With site-to-site deployments, an IPSEC Tunnel is deployed between two gateways, each at the edge of two different remote networks. With remote VPN, an access point (located remotely) defines a tunnel with a security gateway. This facilitates the endpoints in the branch office to communicate with the destination endpoints (behind the security gateway) in a secure manner.
IP Firewall Rules
Lists the IP firewall rules defined for each displayed crypto map configuration. Each firewall policy contains a unique set of access/deny permissions applied to the VPN tunnel and its peer connection.
IPSec Transform Set
Displays the transform set (encryption and has algorithms) applied to each listed crypto map configuration. Thus, each crypto map can be customized with its own data protection and peer authentication schemes.
-
If requiring a new crypto map configuration, select the Add button. If updating the configuration of an existing crypto map, select it from amongst those available and select the Edit button.



