VPLS EAPS Redundancy Overview
To protect your customer access network from link and node failures, you can use the VPLS with Redundant EAPS configuration shown in VPLS with Redundant EAPS Configuration Example.
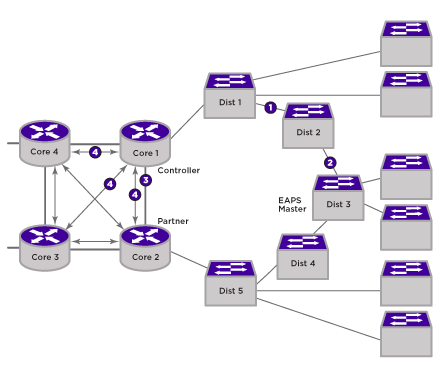
This topology uses redundant VPLS core nodes and an EAPS ring to protect customer access. The redundant VPLS nodes provide protection from the loss of a VPLS node, and the EAPS ring provides protection from the loss of a node or link on the EAPS ring. Within the VPLS nodes, VPLS and EAPS work together to control the use of PWs so that no loops are created.
During normal operation, the Dist2 node is the EAPS ring master, and it blocks the port leading to the link at point 2. The protected VLANs on the EAPS ring do not include the EAPS common link at point 3. The protected VLANS on the EAPS ring use VPLS PWs between the redundant VPLS nodes to connect the two ring segments. This difference in normal EAPS operation is established during configuration by configuring an EAPS-protected VLAN on the core node with only one port on the ring.
To see the commands used to create the configuration shown above, see VPLS with Redundant EAPS Configuration Example.

