DHCP Security Support for MLAG Controlling Bridge
DHCP Security Support for MLAG Controlling Bridge implements the checkpointing of DHCP snooping entries and DHCP and ARP violations between MLAG peers. This allows IP security to share the data or state required for its features, and to exhibit identical behavior in the MLAG topology.
Note
DHCP security for MLAG controlling bridges is also supported in VPEX and W-MLAG topologies.In a typical deployment, a DHCP snooping entry is captured in MLAG Peer1 when it receives a DHCP ACK packet from the DHCP server and forwards it to the DHCP client. The DHCP snoop entry is then checkpointed to MLAG Peer2 as soon as it is received by the IP security module. This ensures redundancy and identical functional behavior in MLAG Peer2 when MLAG Peer1 goes down for any reason:
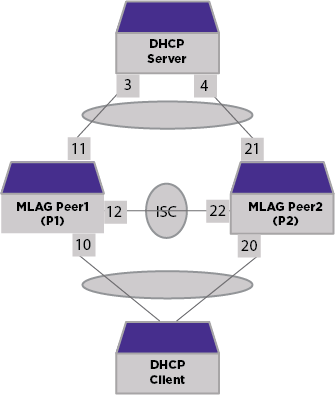
In the following configuration, if a DHCP entry is snooped by Peer1 and checkpointed to Peer2, Peer2 must allow ARP requests arriving on its Port 1 with an IP address that exists in the DHCP snooping database:
MLAG Peer1 configuration
create vlan v1 tag 900 configure vlan v1 add port 10,11,12 tagged enable ip-security dhcp-snooping vlan v1 ports 11 violation-action drop-packet block-port duration 300 enable ip-security arp learning learn-from-dhcp vlan v1 ports 11 enable ip-security arp validation v1 ports 11 violation-action drop-packet block-port duration 300
MLAG Peer2 configuration
create vlan v1 tag 900 configure vlan v1 add port 20,21,22 tagged enable ip-security dhcp-snooping vlan v1 ports 21 violation-action drop-packet block-port duration 300 enable ip-security arp learning learn-from-dhcp vlan v1 ports 21 enable ip-security arp validation v1 ports 21 violation-action drop-packet block-port duration 300
MLAG Checkpointing
After Inter-Switch Connection (ISC) connectivity between the MLAG peers is established, IP security begins checkpointing DHCP snooping and DHCP or ARP violation actions. As long as MLAG peers have ISC connectivity, addition and deletion of entries/data will be checkpointed. The checkpoint is only done for MLAG ports.
DHCP Snoop Checkpointing
When a DHCP snoop entry is checkpointed from Peer1 to Peer2, the receiving peer checks if it has the received DHCP snoop entry present in its DHCP bindings table. If it is a new entry, it will be added to the DHCP binding table with the server ports as ISC ports. The client port is then identified using FDB lookup on the received client MAC. If the receiving entry already exists, the lease time will be updated so that it is in sync with the peer. If the server ports are BPE ports, the checkpoint receiving peer will set to the BPE port as a server instead of an ISC port.
Using the previous configuration example, once a DHCP ACK is received, Peer1 creates a new DHCP snoop entry into its DHCP binding table, with the server port as 11, the client port as 10, and checkpoints the entry to Peer2. On receiving the checkpoint entry, Peer2 adds the entry to its DHCP binding table with the server port as 22 (ISC port) and the client port as 20 (FDB lookup port).
DHCP and ARP Violation Checkpoint
DHCP and ARP Violation events - “block-port” and “block-mac” are checkpointed between MLAG peers for front panel ports. However, violation actions are not applied at the receiving peer. The receiving peer stores the block action, block duration internally, and applies the checkpointed block time (violationTime - lapsedTime) once a similar violation occurs. For example, if Peer1 receives a MAC violation on MAC “00:04:96:97:fa:a2”, then IP security will block the MAC for 300 seconds and checkpoint the information to Peer2. Once the same MAC “00:04:96:97:fa:a2” violation is seen in Peer2 after a period of time, Peer2 will block the MAC for remaining 200 seconds (instead of 300 seconds). This ensures both Peer1 and Peer2 removes or unblocks the violation action at the same time.

Tip
With BPE ports, the violation action is also checkpointed and applied in the peer.
