Management services (Telnet, SSHv2, HTTP, HTTPS and FTP) require administrators enter a valid username and password which is authenticated locally or centrally on a RADIUS server. SNMPv3 also requires a valid username and password which is authenticated by the SNMPv3 module. For CLI and Web UI users, the controller or service platform also requires user role information to know what permissions to assign.
If local authentication is used, associated role information is defined on the controller or service platform when the user account is created.
If RADIUS is used, role information is supplied RADIUS using vendor specific return attributes. If no role information is supplied by RADIUS, the controller or service platform applies default read-only permissions.
Administrators can limit users to specific management interfaces. During authentication, the controller or service platform looks at the user‘s access assignment to determine if the user has permissions to access an interface:
If local authentication is used, role information is defined on the controller or service platform when the user account is created.
If RADIUS is used, role information is supplied by RADIUS using vendor specific return attributes.
The controller or service platform also supports multiple RADIUS server definitions as well as fallback to provide authentication in the event of failure. If the primary RADIUS server is unavailable, the controller or service platform authenticates with the next RADIUS sever, as defined in the AAA policy. If a RADIUS server is not reachable, the controller or service platform can fall back to the local database for authentication. If both RADIUS and local authentication services are unavailable, read-only access can be optionally provided.
The controller or service platform authenticates users using the integrated local database. When user credentials are presented the controller or service platform validates the username and password against the local database and assigns permissions based on the associated roles assigned. The controller or service platform can also deny the authentication request if the user is attempting to access a management interface not specified in the account‘s access mode list.
Use the Administrators tab to review existing administrators, their access medium (type) and administrative role within the controller, service platform or access point managed network. New administrators can be added, and existing administrative user configurations modified or deleted as required.
To create administrators and assign them access types and roles:
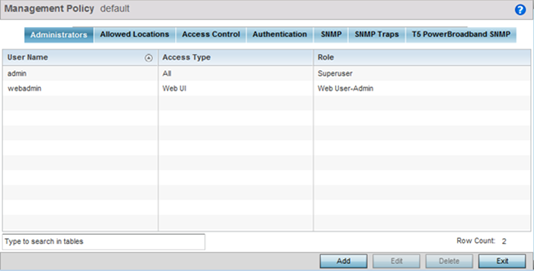
| User Name | Displays the name assigned to the administrator upon creation of their account. The name cannot be modified as part of the administrator configuration edit process. |
| Access Type | Lists the Web UI, Telnet, SSH or Console access type assigned to each listed administrator. A single administrator can have any one (or all) of these roles assigned at the same time. |
| Role | Lists the Superuser, System, Network, Security, Monitor, Help Desk, Web User, Device Provisioning or Vendor Admin role assigned to each listed administrator. An administrator can only be assigned one role at a time. |
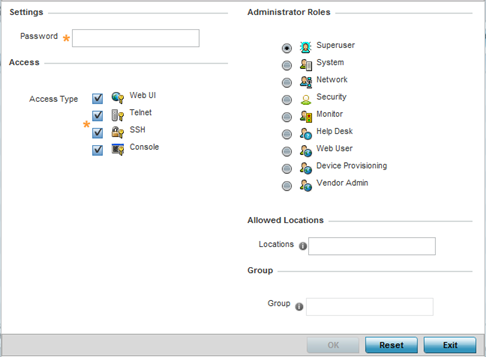
| Web UI | Select this option to enable access to the device‘s Web User Interface. |
| Telnet | Select this option to enable access to the device using TELNET. |
| SSH | Select this option to enable access to the device using SSH. |
| Console | Select this option to enable access to the device‘s console. |
| Superuser | Select this option to assign complete administrative rights to the user. This entails all the roles listed for all the other administrative roles. |
| System | The System role provides permissions to configure general settings like NTP, boot parameters, licenses, perform image upgrades, auto install, manager redundancy/clustering and control access. |
| Network | The Network role provides privileges to configure all wired and wireless parameters like IP configuration, VLANs, L2/L3 security, WLANs, radios, and captive portal. |
| Security | Select Security to set the administrative rights for a security administrator allowing configuration of all security parameters. |
| Monitor | Select Monitor to assign permissions without any administrative rights. The Monitor option provides read-only permissions. |
| Help Desk | Assign this role to someone who typically troubleshoots and debugs problems reported by the customer. The Help Desk manager typically runs troubleshooting utilities (like a sniffer), executes service commands, views and retrieves logs. Help Desk personnel are not allowed to conduct controller or service platform reloads. |
| Web User | Select Web User to assign the administrator privileges needed to add users for authentication. |
| Device Provisioning | Select Device Provisioning to
assign an administrator privileges to update
(provision) device configuration files or
firmware. Such updates run the risk of overwriting
and losing a device‘s existing configuration
unless the configuration is properly
archived. Note:
Starting with WiNG 5.9.4, you can restrict a
device provisioning admin's access to
specific location or locations by applying
the Allowed Locations tag. When
applied, this user, will only have access to
devices within the locations (RF
Domains/sites/tree-node paths) associated
with the allowed-locations tag.
Note: For information on configuring the
allowed-locations tag, click here.
|
| Vendor Admin | Select this option to create a vendor-admin user role group so
this particular user type can access offline device-registration
portal data. Vendors are assigned username/password credentials for
securely on boarding devices. Devices are moved to a vendor allowed
VLAN immediately after this on-boarding process, so vendors do require
unique administration roles. When the Vendor-Admin role is selected,
provide the vendor‘s Group name for RADIUS authentication. The
vendor's RADIUS group takes precedence over the statically configured
group for device registration. Note: The Allowed Locations option is
not applicable to this role.
|