Override General Security Settings
About this task
A profile can make use of existing firewall, wireless client role, and WIPS policies and apply them to the profile‘s configuration. This affords each profile a truly unique combination of data protection policies for best meeting the data protection requirements of the profile it supports. However, as deployment requirements arise, an individual device may need some or all of its general security configuration overridden from the profile‘s settings.
To configure a profile‘s security settings and overrides:
Procedure
-
Select Configuration > Devices from the web UI.
The Device Configuration screen displays a list of managed devices or peer controllers, service platforms, or access points.
-
Select a target device in the lower left-hand side of the UI.
You can also select a target device by double-clicking it in the list in the Device Configuration screen.
- Select Profile Overrides → Security.
-
Select Settings.
 Device Overrides - Security Settings Screen
Device Overrides - Security Settings Screen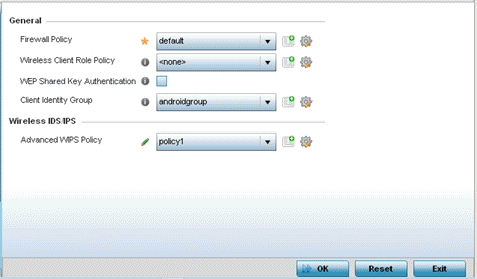
Note
A blue override icon (to the left of a parameter) defines the parameter as having an override applied. To remove an override go to the Basic Configuration section of the device and click Clear Overrides. This removes all overrides from the device. -
Refer to the General field to
assign or override the following:
Firewall Policy Select an existing Firewall policy to use as an additional security mechanism with a profile. All devices using this profile must meet the requirements of the firewall policy to access the network. A firewall is a mechanism enforcing access control, and is considered a first line of defense in protecting proprietary information within the network. The means by which this is accomplished varies, but in principle, a firewall can be thought of as mechanisms that both block and permit data traffic within the network. If an existing firewall policy does not meet your requirements, click the Create icon to create a new firewall policy that can be applied to this profile. An existing policy can also be selected and overridden as needed using the Edit icon.
Wireless Client Role Policy Select a client role policy used to strategically filter client connections based on a pre-defined set of filter rules and connection criteria. If an existing Wireless Client Role policy does not meet your requirements, click the Create icon to create a new firewall policy that can be applied to this profile. An existing policy can also be selected and overridden as needed using the Edit icon. WEP Shared Key Authentication Select this option to require devices to use a WEP key to access the network using this profile.
The controller or service platform uses the key algorithm to convert an ASCII string to the same hexadecimal number.
Clients without adapters need to use WEP keys manually configured as hexadecimal numbers. This option is disabled by default.
Client Identity Group Select the client identity group to apply to this device profile. Client identity is a set of unique fingerprints used to identify a class of devices. A client identity group is a set of client attributes that identify devices and apply specific permissions and restrictions on them. The information is used to configure permissions and access rules for that device class and can assist administrators by applying permissions and rules to multiple devices simultaneously.
CMP Policy Use the drop down-menu to assign a CMP policy to allow a device to communicate to a CMP supported CA server, initiate a certificate request and download the required certificates from the CA server. CMP supports multiple request options through for device communicating to a CMP supported CA server. The device can initiate a request for getting the certificates from the server. It can also auto update the certificates which are about to expire.
-
Use the URL Filter
drop-down menu to select or override the URL Filter configuration applied to
this virtual interface.
URL filtering is used to restrict access to resources on the internet.
-
Click OK to save the
changes or overrides.
Click Reset to revert to the last saved configuration.
