Configuring an LDAP Server Configuration
RADIUS is not just a database. It's a protocol for asking intelligent questions to a user database (like LDAP). LDAP however is just a database of user credentials that can be used optionally with the RADIUS server to free up resources and manage user credentials from a secure remote location. Local controller, service platform or access point RADIUS resources provide the tools to perform user authentication and authorize users based on complex checks and logic. There's no way to perform such complex authorization checks from a LDAP user database alone.
To configure an LDAP server configuration for use with the RADIUS server:
- Select the LDAP tab from the
RADIUS Server screen.RADIUS Server Policy Screen - LDAP Tab

Note
If you are using LDAP for external authentication, PEAP-MSCHAPv2 can be used only if the LDAP server returns the password as plain text. PEAP-MSCHAPv2 is not supported if the LDAP server returns encrypted passwords. This restriction does not apply for Microsoft's Active Directory Server. -
Refer to the following to determine whether an LDAP server can be used as is, a server configuration requires creation or modification, or a configuration requires deletion and permanent removal.
Redundancy Displays whether the listed LDAP server IP address has been defined as a primary or secondary server resource. Designating at least one secondary server is a good practice to ensure RADIUS resources are available if a primary server were to become unavailable. IP Address Displays the IP address of the external LDAP server acting as the data source for the RADIUS server. Port Lists the physical port number used by the RADIUS server to secure a connection with the remote LDAP server resource. Timeout Lists the number of seconds (1- 10) this server session waits for a connection before aborting the connection attempt with the listed RADIUS server resource. - Click Add to add a new LDAP server configuration, Edit to modify an existing LDAP
server configuration, or Delete to remove a LDAP server from the list of those available.LDAP Server Add Screen
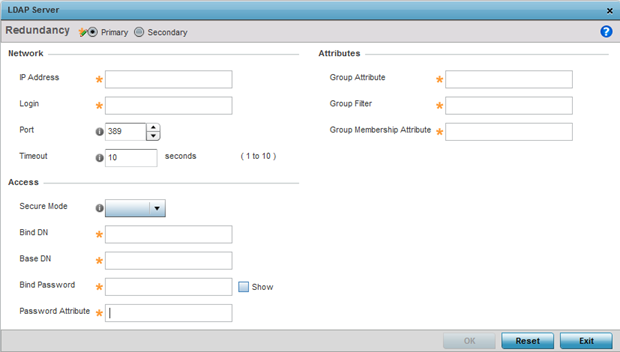
- Set the following Network address information required for the connection to an
external LDAP server resource:
Redundancy Define whether this LDAP server is a primary or secondary server resource. Primary servers are always queried for connection first. However, designating at least one secondary server is a good practice to ensure RADIUS user information is available if a primary server were to become unavailable. IP Address Set the 128-character maximum IP address or FQDN of the external LDAP server acting as the data source for the RADIUS server. Login Define a unique login name used for accessing the remote LDAP server resource. Consider using a unique login name for each LDAP server provided to increase the security of the connection to the remote LDAP server. Port Use the spinner control to set the physical port number used by the RADIUS server to secure a connection with the remote LDAP server. Timeout Set an interval from 1 - 10 seconds the local RADIUS server uses as a wait period for a response from the primary or secondary LDAP server. The default setting is 10 seconds. - Set the following Access address information required for the connection to the
external LDAP server resource:
Secure Mode Specify the security mode when connecting to an external LDAP server. Use start-tls or tls-mode to connect. The start-tls mode provides a way to upgrade a plain text connection to an encrypted connection using TLS. The default port value for start-tls is 389. The default port value for stls-mode is 636. Bind DN Specify the distinguished name to bind with the LDAP server. The DN is the name that uniquely identifies an entry in the LDAP directory. A DN is made up of attribute value pairs, separated by commas. Base DN Specify a distinguished name (DN) that establishes the base object for the search. The base object is the point in the LDAP tree at which to start searching. LDAP DNs begin with the most specific attribute (usually some sort of name), and continue with progressively broader attributes, often ending with a country attribute. The first component of the DN is referred to as the Relative Distinguished Name (RDN). It identifies an entry distinctly from any other entries that have the same parent. Bind Password Enter a valid password for the LDAP server. Select the Show checkbox to expose the password‘s actual character string, leaving the option unselected displays the password as a string of asterisks (*). The password cannot exceed 32 characters. Password Attribute Enter the LDAP server password attribute. The password cannot exceed 64 characters. - Set the following Attributes for LDAP groups to optimally refine group queries:
GroupAttribute LDAP systems have the facility to poll dynamic groups. In an LDAP dynamic group, an administrator can specify search criteria. All users matching the search criteria are considered a member of this dynamic group. Specify a group attribute used by the LDAP server. An attribute could be a group name, group ID, password, or group membership name. Group Filter The group filters used by the LDAP server. This filter is typically used for security role-to-group assignments and specifies the property to look up groups in the directory service. Group Membership Attribute The group member attribute sent to the LDAP server when authenticating users. - Click OK to save the changes to the LDAP server configuration. Click Reset to revert to the last saved configuration.

