Overriding Security Configuration
About this task
Use this screen to configure firewalls. The firewall inspects packet traffic to and from connected clients. If there is no firewall rule that meets the data protection needs of this virtual interface, select the Create icon to define a new firewall rule configuration or the Edit icon to modify or override an existing configuration. For more information, see Wireless Firewall.
To override the VLAN security configuration:
Procedure
-
Select the Security
tab.
 Profile Overrides - Virtual Interfaces Security Screen
Profile Overrides - Virtual Interfaces Security Screen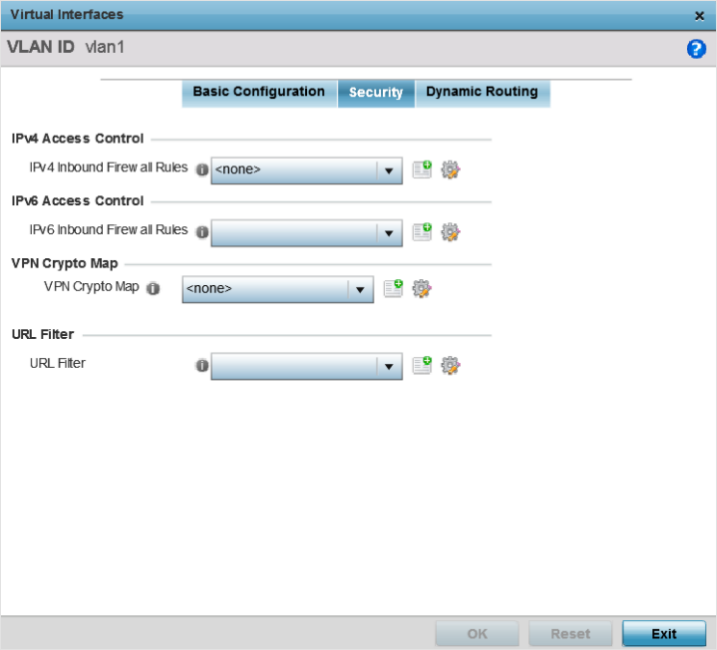
-
Use the IPv4 Inbound Firewall
Rules drop-down menu to select the IPv4 specific inbound
firewall rules to apply to this profile‘s virtual interface configuration.
Click the Create icon to define a new IPv4 firewall rule configuration, or click the Edit icon to modify an existing configuration.
IPv4 is a connectionless protocol for packet switched networking. IPv4 operates as a best effort delivery method, since it does not guarantee delivery, and does not ensure proper sequencing or duplicate delivery (unlike (TCP).
IPv4 and IPv6 are different enough to warrant separate protocols. IPv6 devices can alternatively use stateless address autoconfiguration. IPv4 hosts can use link local addressing to provide local connectivity.
-
Use the IPv6 Inbound Firewall
Rules drop-down menu to select the IPv6 specific inbound
firewall rules to apply to this profile‘s virtual interface configuration.
Click the Create icon to define a new IPv6 firewall rule configuration, or click the Edit icon to modify an existing configuration.
IPv6 is the latest revision of the Internet Protocol replacing IPv4. IPV6 provides enhanced identification and location information for systems routing traffic across the Internet. IPv6 addresses are composed of eight groups of four hexadecimal digits separated by colons. For more information on creating IPv6 firewall rules, see Configuring IP Firewall Rules.
-
Use the VPN Crypto Map
drop-down menu to select or override the Crypto Map configuration applied to
this virtual interface.
Crypto Map entries are sets of configuration parameters for encrypting packets that pass through the VPN Tunnel. If there is no Crypto Map configuration that meets the needs of this virtual interface, click the Create icon to define a new Crypto Map configuration or click the Edit icon to modify an existing configuration. For more information, see Overriding VPN Configuration.
-
Use the
URL
Filter drop-down menu to select or override
the URL
Filter configuration applied to this virtual
interface.
URL filtering is used to restrict access to undesirable resources on the internet.
-
Click OK to save the
changes and overrides to the Security screen.
Click Reset to revert to the last saved configuration.


