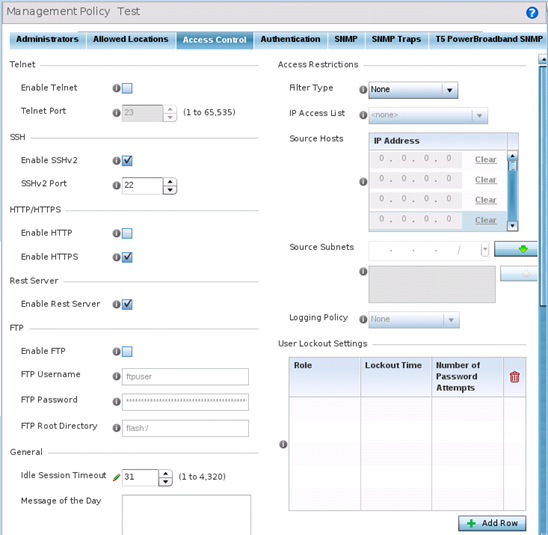
Setting the Access Control Configuration
About this task
Restricting remote access to a controller or service platform ensures only trusted hosts can communicate with enabled management services. This ensures only trusted hosts can perform management tasks and provide protection from brute force attacks from hosts attempting to break into the controller or service platform managed network.
Administrators can permit management connections to be established on any IP interface on the controller or service platform (including IP interfaces used to provide captive portal guest access). Administrators can restrict management access by limiting access to a specific host (IP address), subnet, or ACL on the controller or service platform.
Refer to the Access Control screen to allow/deny management access to the network using strategically selected protocols (HTTP, HTTPS, Telnet, SSH or SNMP). Access options can be either enabled or disabled as required. Consider disabling unused interfaces to close unnecessary security holes. The Access Control tab is not meant to function as an ACL (in routers or other firewalls), where you can specify and customize specific IPs to access specific interfaces.
-
Source hosts - Management access can be restricted to one or more hosts by specifying their IP addresses
-
Source subnets - Management access can be restricted to one or more subnets
-
IP ACL - Management access can be based on the policies defined in an IP based ACL
In the following example, a controller has two IP interfaces defined with VLAN10 hosting management and network services and VLAN70 providing guest services. For security the guest network is separated from all trusted VLANs by a firewall.
| Interface | Description | IP Address | Management |
|---|---|---|---|
| VLAN10 | Services | Yes | Yes |
| VLAN70 | Guest | Yes | No |
By default, management services are accessible on both VLAN10 and VLAN70, and that‘s not desirable to an administrator. By restricting access to VLAN10, the controller only accepts management sessions on VLAN10. Management access on VLAN70 is longer available.
Administrators can secure access to a controller or service platform by disabling less secure interfaces. By default, the CLI, SNMP and FTP disable interfaces that do not support encryption or authentication. However, Web management using HTTP is enabled. Insecure management interfaces such as Telnet, HTTP and SNMP should be disabled, and only secure management interfaces, like SSH and HTTPS should be used to access the controller or service platform managed network.
The following table demonstrates how some interfaces provide better security than others:
| Access Type | Encrypted | Authenticated | Default State |
|---|---|---|---|
| Telnet | No | Yes | Disabled |
| SNMPv2 | No | No | Enabled |
| SNMPv3 | Yes | Yes | Enabled |
| HTTP | No | Yes | Disabled |
| HTTPS | Yes | Yes | Disabled |
| FTP | No | Yes | Disabled |
| SSHv2 | Yes | Yes | Disabled |
To set an access control configuration for the Management Access policy: