Sending standard 802.11 deauthentication frames to prevent stations from associating to threat devices.
Rate limiting flooded frames. This can prevent floods from propagating through the AP to the wired network.
Blacklisting attacking devices to prevent them from gaining access to the network.
Countermeasures are enabled on a per-scan-profile basis. Some scan profiles can have countermeasures enabled while others cannot.
To select a specific countermeasure:
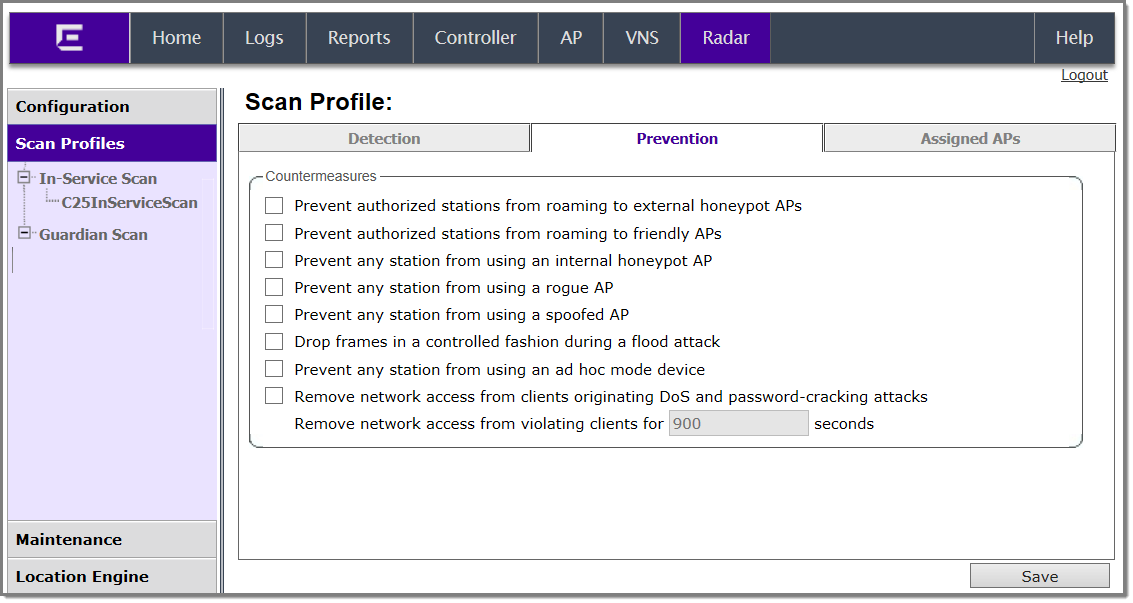
Prevention Tab - Fields and Buttons
| Field/Button | Description |
|---|---|
| Countermeasures | |
| Prevent authorized stations from roaming to external honeypot APs | An external honeypot is an AP that is attempting to make itself a man-in-the-middle by advertising a popular SSID, such as an SSID advertised by a coffee shop or an airport |
| Prevent authorized stations from roaming to friendly APs | Friendly APs are APs that are not part of the authorized wireless network, but they operate in the vicinity of the authorized wireless network. |
| Prevent any station from using an internal honeypot AP | An internal honeypot is an AP that is attempting to make itself a man-in-the-middle by advertising an SSID belonging to the authorized network. |
| Prevent any station from using a rogue AP | A rogue AP is an unauthorized AP connected to the authorized wired network. |
| Prevent any station from using a spoofed AP | A spoofed AP is an AP that is not part of the authorized network is advertising a BSSID (MAC address) that belongs to an authorized AP on the authorized network. |
| Drop frames in a controlled fashion during a flood attack | Prevents some types of Denial of Service (DoS) attack from affecting the authorized network instead of just the target AP. For example, rate limiting the flooded frames. |
| Prevent any station from using an ad hoc mode device | Deauthentication messages are used to prevent devices from using an ad hoc mode device. |
| Remove network access from clients originating DoS and password-cracking attacks | Prevents propagation of the DoS attack from the
AP to the authorized network. Many types of DoS attack involve
deluging an AP with a large volume of messages of one or two specific
types. When this option is enabled, the AP will apply rate limits to
the specific type of frame that is being deluged. The selected clients for this countermeasure are denied access to the network for the amount of time that is specified in " Remove network access from violating clients for a period of time." |
| Remove network access from violating clients for a period of time | Enter a numeric value in seconds. |
| New | Click to create a new scan profile. For more information, see Adding a New Scan Profile. |
| Delete | Click to delete the selected scan profile. |
| Save | Click to save changes. |