This section describes the commands available within a device's CLI structure. CLI is available for access points, wireless controller, and service platforms.
You can access the CLI by using:
If connecting through the serial port, use the following settings to configure your terminal emulator:
| Bits Per Second |
19200 - For NX5500, NX7500, NX9500, NX9600, VX9000 model service platforms. 115200 - For AP505 and AP510 model access points |
| Data Bits | 8 |
| Parity | None |
| Stop Bit | 1 |
| Flow Control | None |
When a CLI session is established, complete the following (user input is in bold):
login as: <username> administrator's login password: <password>
Use the following credentials when logging into a device for the first time:
| User Name | admin |
| Password | admin123 |
When logging into the CLI for the first time, you are prompted to change the password. Reset the password and use it for subsequent logins.
Examples used in this reference guide are generic to the each supported wireless controller, service platform, and AP model. Commands that are not common, are identified using the notation "Supported in the following platforms." For an example, see below:
Supported in the following platforms:
The above example indicates the command is only available for a NX 5500 model wireless controller.
The CLI is used for configuring, monitoring, and maintaining the network. The user interface allows you to execute commands on supported wireless controllers, service platforms, and APs, using either a serial console or a remote access method.
This chapter describes basic CLI features. Topics covered include an introduction to command modes, navigation and editing features, help features and command history.
The CLI is segregated into different command modes. Each mode has its own set of commands for configuration, maintenance, and monitoring. The commands available at any given time depend on the mode you are in, and to a lesser extent, the particular model used. Enter a question mark (?) at the system prompt to view a list of commands available for each command mode/instance.
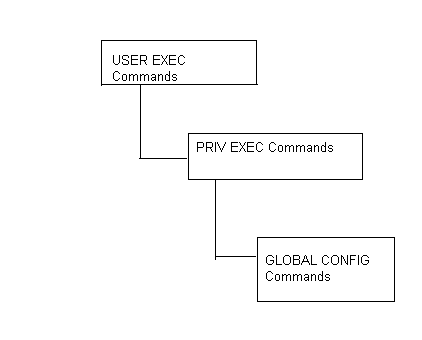
Use specific commands to navigate from one command mode to another. The standard order is: USER EXEC mode, PRIV EXEC mode and GLOBAL CONFIG mode.
A session generally begins in the USER EXEC mode (one of the two access levels of the EXEC mode). For security, only a limited subset of EXEC commands are available in the USER EXEC mode. This level is reserved for tasks that do not change the device‘s (wireless controller, service platform, or AP) configuration.
ap505-13403B>
The system prompt signifies the device name and the last three bytes of the device MAC address.
To access commands, enter the PRIV EXEC mode (the second access level for the EXEC mode). Once in the PRIV EXEC mode, enter any EXEC command. The PRIV EXEC mode is a superset of the USER EXEC mode.
ap505-13403B>en ap505-13403B#
Most of the USER EXEC mode commands are one-time commands and are not saved across device reboots. Save the command by executing ‘commit‘ command. For example, the show command displays the current configuration and the clear command clears the interface.
Access the GLOBAL CONFIG mode from the PRIV EXEC mode. In the GLOBAL CONFIG mode, enter commands that set general system characteristics. Configuration modes, allow you to change the running configuration. If you save the configuration later, these commands are stored across device reboots.
Access a variety of protocol specific (or feature-specific) modes from the global configuration mode. The CLI hierarchy requires you to access specific configuration modes only through the global configuration mode.
ap505-13403B#configure terminal Enter configuration commands, one per line. End with CNTL/Z. ap505-13403B(config)#
You can also access sub-modes from the global configuration mode. Configuration sub-modes define specific features within the context of a configuration mode.
ap505-13403B(config)#aaa-policy test ap505-13403B(config-aaa-policy-test)#
ap505-13403B(config)#self ap505-13403B(config-device-94-9B-2C-13-40-38)#
The following table summarizes the available controller commands:
Controller CLI Modes and Commands
| User Exec Mode | Priv Exec Mode | Global Configuration Mode |
|---|---|---|
| captive-portal-page-upload | archive | aaa-policy |
| change-passwd | boot | aaa-tacacs-policy |
| clear | captive-portal-page-upload | alias |
| clock | cd | AP505 |
| cluster | change-passwd | AP510 |
| commit | clear | application |
| connect | clock | application-group |
| create-cluster | cluster | application-policy |
| crypto | commit | association-acl-policy |
| crypto-cmp-cert-update | configure | auto-provisioning-policy |
| database | connect | bgp |
| database-backup | copy | ble-data-export-policy |
| database-restore | cpe (supported on NX7500, NX9500, NX9600, and VX9000) | bonjour-gw-discovery-policy |
| debug | create-cluster | bonjour-gw-forwarding-policy |
| device-upgrade | crypto | bonjour-gw-query-forwarding-policy |
| disable | crypto-cmp-cert-update | captive-portal |
| enable | database | clear |
| file-sync | database-backup | client-identity |
| help | database-restore | client-identity-group |
| join-cluster | debug | clone |
| l2tpv3 | delete | crypto-cmp-policy |
| logging | device-upgrade | customize |
| mint | diff | database-client-policy (supported only on VX9000) |
| no | dir | database-policy (supported only on NX9500, NX9600, and VX9000) |
| on | disable | device |
| opendns | edit | device-categorization |
| page | dhcp-server-policy | |
| ping | enable | dhcpv6-server-policy |
| ping6 | erase | dns-whitelist |
| revert | ex3500 (supported only on NX9500, NX9600, and VX9000) | event-system-policy |
| service | factory-reset | ex3500 |
| show | file-sync | ex3500-management-policy |
| ssh | halt | ex3500-qos-class-map-policy |
| telnet | help | ex3500-qos-policy-map |
| terminal | join-cluster | ex3524 |
| time-it | l2tpv3 | ex3548 |
| traceroute | logging | firewall-policy |
| traceroute6 | mint | global-association-list |
| virtual-machine (supported only on NX9500, NX9600, and VX9000) | mkdir | guest-management |
| watch | more | help |
| write | no | host |
| clrscr | on | igmp-snoop-policy (This command has been deprecated. IGMP snooping is now configurable under the profile/device configuration mode. For more information, see ip. |
| exit | opendns | inline-password-encryption |
| page | iot-device-type-imagotag-policy | |
| ping | ip | |
| ping6 | ipv6 | |
| pwd | ipv6-router-advertisement-policy | |
| raid (supported only on NX9500, NX9600, and NX7500) | l2tpv3 | |
| re-elect | location-policy | |
| reload | mac | |
| remote-debug | management-policy | |
| rename | meshpoint | |
| revert | meshpoint-qos-policy | |
| rmdir | mint-policy | |
| self | nac-list | |
| service | no | |
| set-personality | nsight-policy | |
| show | NX5500 (supported only on NX9500, NX9600, and VX900 and ) | |
| ssh | NX7500 (supported only on NX9500, NX9600, and VX9000) | |
| t5 (supported only on RFS400, NX9500, NX9600, and VX9000) | NX9000 (supported only on NX9500, NX9600, and VX9000) | |
| telnet | NX9600 (supported only on NX9600, and VX9000) | |
| terminal | passpoint-policy | |
| time-it | password-encryption | |
| traceroute | profile | |
| traceroute6 | radio-qos-policy | |
| upgrade | radius-group | |
| upgrade-abort | radius-server-policy | |
| virtual-machine (supported only on NX9500, NX9600 and VX9000) | radius-user-pool-policy | |
| watch | rename | |
| replace | ||
| write | rf-domain | |
| clrscr | rfs4000 | |
| exit | roaming-assist-policy | |
| role-policy | ||
| route-map | ||
| routing-policy | ||
| rtl-server-policy | ||
| schedule-policy | ||
| self | ||
| sensor-policy | ||
| smart-rf-policy | ||
| t5 (supported only on NX7500, NX9500, NX9600 and VX9000 | ||
| url-filter (supported only on NX9500, NX9600, and VX9000) | ||
| url-list (supported only on NX9500, NX9600 and VX9000) | ||
| vx9000 (supported only on NX9500, NX9600, and VX9000) | ||
| web-filter-policy | ||
| wips-policy | ||
| wlan | ||
| wlan-qos-policy | ||
| write | ||
| clrscr | ||
| commit | ||
| do | ||
| end | ||
| exit | ||
| revert | ||
| service | ||
| show |