To define a bridge VLAN general configuration:
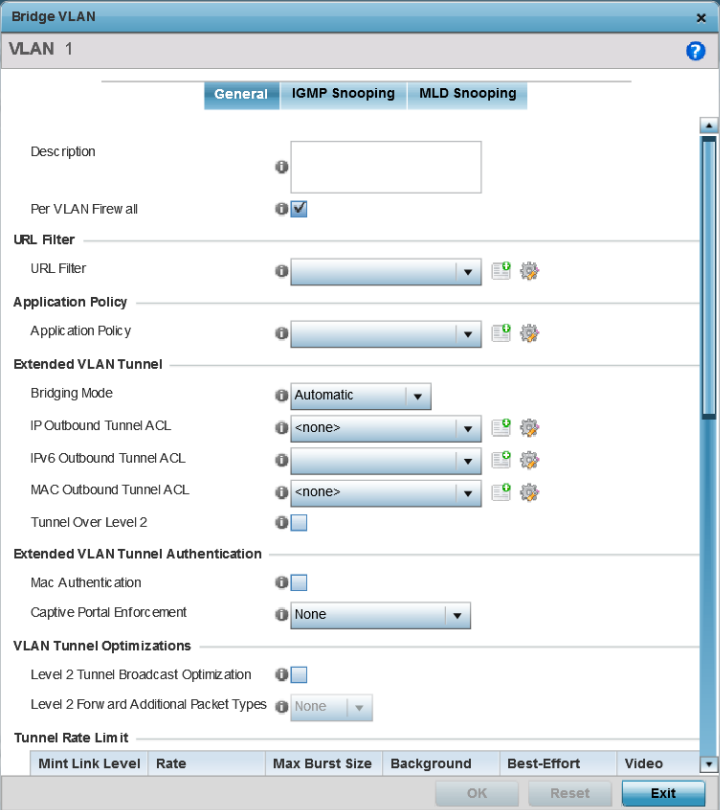
The General tab displays by default.
If adding a new Bridge VLAN configuration, use the spinner control to define a VLAN ID between 1 - 4094. This value must be defined and saved before the General tab can become enabled and the remainder of the settings defined. VLAN IDs 0 and 4095 are reserved and unavailable.
Set the following general bridge VLAN parameters:
|
Description |
If creating a new Bridge VLAN, provide a description (up to 64 characters) unique to the VLAN's specific configuration to help differentiate it from other VLANs with similar configurations. |
|
Per VLAN Firewall |
Enable this setting to provide firewall allow and deny conditions over the bridge VLAN. This setting is enabled by default. |
|
URL Filter |
Use the drop-down menu to select a URL filter to use with this Bridge VLAN. |

Note
The WiNG 7.1.X release does not support third-party DPI engine on the AP5XX model access points. WiNG 7.1.2 supports EAA (Extreme Application Analytics) (Purview™) DPI engine on the WiNG 7.1.X APs. For more information, refer the WiNG 7.1.2 CLI Reference guide, available at https://extremenetworks.com/documentation.Set the following Extended VLAN Tunnel parameters:
|
Bridging Mode |
Specify one of the following bridging modes for the VLAN. Automatic: Select automatic to let the controller, service platform or access point determine the best bridging mode for the VLAN. Local: Select Local to use local bridging mode for bridging traffic on the VLAN. Tunnel: Select Tunnel to use a shared tunnel for bridging traffic on the VLAN. isolated-tunnel: Select isolated-tunnel to use a dedicated tunnel for bridging VLAN traffic. |
|
IP Outbound Tunnel ACL |
Select an IP Outbound Tunnel ACL for outbound traffic from the drop-down menu. If an appropriate outbound IP ACL is not available, select the Create button to make a new one. |
|
MAC Outbound Tunnel ACL |
Select a MAC Outbound Tunnel ACL for outbound traffic from the drop-down menu. If an appropriate outbound MAC ACL is not available click the Create button to make a new one. |
|
Tunnel Over Level 2 |
Select this option to allow VLAN traffic to be tunneled over level 2 links. This setting is disabled by default. |

Note
Local and Automatic bridging modes do not work with ACLs. ACLs can only be used with tunnel or isolated-tunnel modes.
|
MAC Authentication |
Select to enable source MAC authentication for extended VLAN and tunneled traffic (MiNT and L2TPv3) on this bridge VLAN. When enabled, it provides fast path authentications of clients, whose captive portal session has expired. This option is disabled by default. |
|
Captive-Portal Authentication |
Use the drop-down menu to specify authentication mode used for extended VLAN and tunneled traffic, on this Bridge VLAN. The options are: None – No Authentication mode used. This is the default setting. Authentication Failure – Configures MAC Authentication as the primary and Captive-Portal Authentication as the fall-back authentication mode. Always – Configures Captive-Portal Authentication as the only mode of Authentication |
|
Edge VLAN Mode |
Select this option to enable edge VLAN mode. When selected, the edge controller's IP address in the VLAN is not used, and is now designated to isolate devices and prevent connectivity. This feature is enabled by default. |
Set the following Layer 2 Firewall parameters:
|
Trust ARP Response |
Select this option to use trusted ARP packets to update the DHCP Snoop Table to prevent IP spoof and arp-cache poisoning attacks. This feature is disabled by default. |
|
Trust DHCP Responses |
Select this option to use DHCP packets from a DHCP server as trusted and permissible within the managed network. DHCP packets are used to update the DHCP Snoop Table to prevent IP spoof attacks. This feature is disabled by default. |
|
Edge VLAN Mode |
Select this option to enable edge VLAN mode. When selected, the edge controller's IP address in the VLAN is not used, and is now designated to isolate devices and prevent connectivity. This feature is enabled by default. |
Select the OK button to save the changes to the General tab. Select Reset to revert to the last saved configuration.