The encryption method is TKIP (Temporal Key Integrity Protocol). TKIP addresses WEP's weaknesses with a re-keying mechanism, a per-packet mixing function, a message integrity check and an extended initialization vector. However, TKIP also has vulnerabilities.
CCMP is a security standard used by the AES (Advanced Encryption Standard). AES serves the same function TKIP does for WPA-TKIP. CCMP computes a MIC (Message Integrity Check) using the proven CBC (Cipher Block Chaining) technique. Changing just one bit in a message produces a totally different result.
To configure TKIP-CCMP encryption on a WLAN:
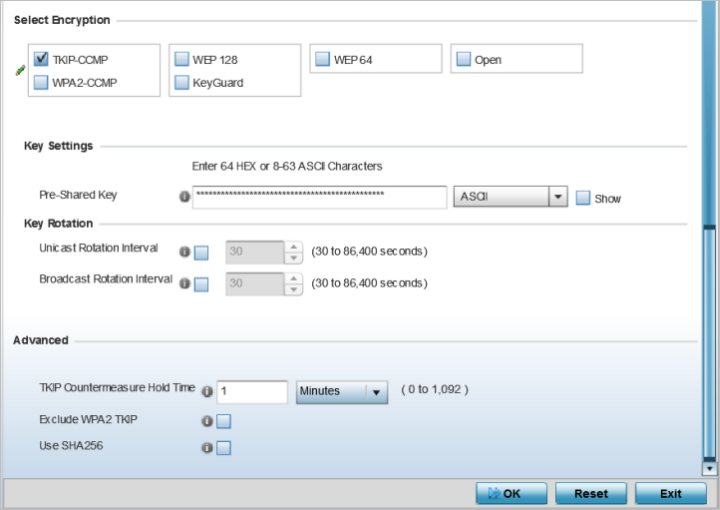
| Pre-Shared Key | Enter either an alphanumeric string of 8 to 63 ASCII characters or 64 HEX characters as the primary string both transmitting and receiving authenticators must share. The alphanumeric string allows character spaces. The string is converetd to to a numeric value. This passphrase saves the administrator from entering the 256-bit key each time keys are generated. |
Rotating the keys is recommended the keys so a potential hacker would not have enough data using a single key to attack the deployed encryption scheme.
| Unicast Rotation Interval | Define an interval for unicast key transmission interval from 30 - 86,400 seconds. Some clients have issues using unicast key rotation, so ensure you know which kind of clients are impacted before using unicast keys. This feature is disabled by default. |
| Broadcast Rotation Interval | When enabled, the key indices used for encrypting and decrypting broadcast traffic is alternatively rotated based on the defined interval. Define a broadcast key transmission interval from 30 - 86,400 seconds. Key rotation enhances the broadcast traffic security on the WLAN. This feature is disabled by default. |

Note
Fast Roaming is available only when the authentication is EAP or EAP-PSK and the selected encryption is either TKIP-CCMP or WPA2-CCMP.Using 802.11i can speed up the roaming process from one access point to another. Instead of doing a complete 802.1x authentication each time a client roams between access points, 802.11i allows a client to re-use previous PMK authentication credentials and perform a four-way handshake. This speeds up the roaming process. In addition to reusing PMKs on previously visited access points, Opportunistic Key Caching allows multiple access points to share PMKs among themselves. This allows a client to roam to an access point it has not previously visited and reuse a PMK from another access point to skip 802.1x authentication.
| Pre-Authentication | Selecting this option enables an associated client to carry out an 802.1x authentication with another access point before it roams to it. This enables a roaming client to send and receive data sooner by not having to conduct an 802.1x authentication after roaming. With pre-authentication, a client can perform an 802.1X authentication with other detected access points while still connected to its current access point. When a device roams to a neighboring access point, the device is already authenticated on the access point, thus providing faster re-association. |
| Pairwise Master Key (PMK) Caching | Pairwise Master Key (PMK) caching is a technique for sidestepping the need to re-establish security each time a client roams to a different switch. Using PMK caching, clients and switches cache the results of 802.1X authentications. Therefore, access is much faster when a client roams back to a switch to which the client is already authenticated. |
| Opportunistic Key Caching | This option enables the access point to use a PMK derived with a client on one access point, with the same client when it roams over to another access point. Upon roaming, the client does not have to do 802.1x authentication and can start sending and receiving data sooner. |
| TKIP Countermeasure Hold Time | The TKIP Countermeasure Hold Time is the time a WLAN is disabled, if TKIP countermeasures have been invoked on the WLAN. Use the drop-down menu to define a value in either Hours (0-18), Minutes (0-1,092) or Seconds (0-65,535). The default setting is 1 second. |
| Exclude WPA2-TKIP | Select this option to advertise and enable support for only WPA-TKIP. This option can be used if certain older clients are not compatible with newer WPA2-TKIP information elements. Enabling this option allows backwards compatibility for clients that support WPA-TKIP and WPA2-TKIP, but do not support WPA2-CCMP. We recommend that you enable this feature if WPA-TKIP or WPA2-TKIP supported clients operate in a WLAN populated by WPA2- CCMP enabled clients. This feature is disabled by default. |
| Use SHA256 |
Select this option to enable SHA-256 authentication key management suite. This suite consists of a set of algorithms for key agreement, key derivation, key wrapping, and content encryption and provide a minimum cryptographic security level of 128 bits. This feature is disabled by default. |
Select Reset to revert to the last saved configuration.