CMP (Certificate Management Protocol) is an Internet protocol to obtain and manage digital certificates in a PKI (Public Key Infrastructure) network. A CA (Certificate Authority) issues the certificates using the defined CMP.
Using CMP, a device can communicate to a CMP supported CA server, initiate a certificate request and download the required certificates from the CA server. CMP supports multiple request options through for device communicating to a CMP supported CA server. The device can initiate a request for getting the certificates from the server. It can also auto update the certificates which are about to expire.
The CMP client on the controller, service platform or Access Point triggers a request for the configured CMS CA server. Once the certificate is validated and confirmed from the CA server it is saved on the device and becomes part of the trustpoint. During the creation of the CMP policy the trustpoint is assigned a name and client information. An administrator can use a manually created trustpoint for one service (like HTTPs) and use the CMP generated trustpoint for RADIUS EAP certificate based authentication.
To review, create or edit a Crypto CMP policy:
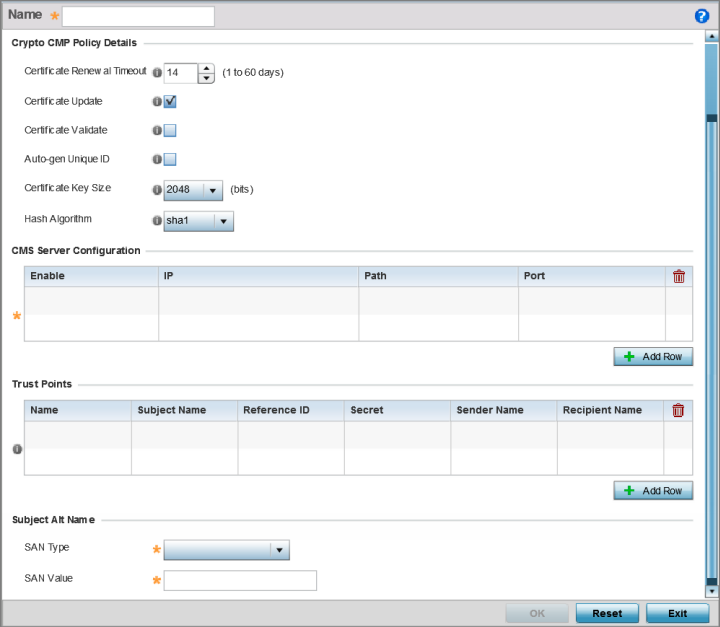
| Enable | Use the drop-down menu to set the CMS server as either the Primary (first choice) or Secondary (secondary option) CMP server resource. |
| IP | Define the IP address for the CMP CA server managing digital certificate requests. CMP certificates are encrypted with CA's public key and transmitted to the defined IP destination over a typical HTTP or TLS session. |
| Path | Provide a complete path to the CMP CA‘s trustpoint. |
| Port | Provide a CMP CA port number. |
| Name | Enter the 32 character maximum name assigned to the target trustpoint. A trustpoint represents a CA/identity pair containing the identity of the CA, CA specific configuration parameters, and an association with an enrolled identity certificate. This field is mandatory. |
| Subject Name | Provide a subject name of up to 512 characters for the certificate template example. This field is mandatory. |
| Reference ID | Set the user reference value for the CMP CA trust point message. The range is 0-256. This field is mandatory. |
| Secret | Specify the secret used for trustpoint authentication over the designated CMP server resource. |
| Sender Name | Enter a sender name up to 512 characters for the trustpoint request. This field is mandatory. |
| Recipient Name | Enter a recipient name value of up to 512 characters for the trustpoint request. |
| SAN Type | Use the drop-down menu to set the Subject Alt Name type as either IP Address, Distinguished Name, Email, String, or FQDN. This field is mandatory. |
| SAN Value | Provide a Subject Alt Name value of up to 128 characters for the certificate template example. The value provided depends on the Subject Alt Name type selected. This field is mandatory. |