To define or override the access point profile's miscellaneous settings:
The miscellaneous settings configuration screen displays.
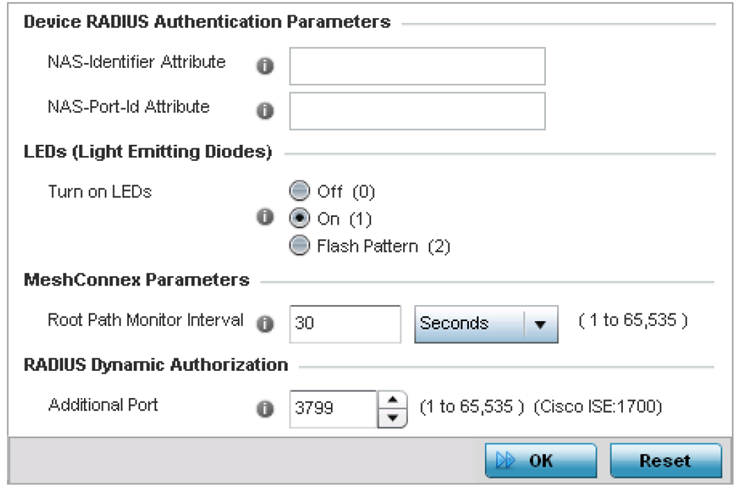
This is the RADIUS NAS-Identifier attribute that typically identifies where a RADIUS message originates.
This is the RADIUS NAS port ID attribute which identifies the device port where a RADIUS message originates.
Off (0) - select to disable LEDs on the access point.
On (1) - select to enable LEDs on an access point.

Note
This is the default setting.
Flash Pattern (2) - to enable the access point to blink in a manner different from its operational LED behavior.

Note
Enabling this option allows an administrator to validate that the access point has received its configuration from its managing controller during staging. In the staging process, the administrator adopts the access point to a staging controller to get an initial configuration before the access point is deployed at its intended location. Once the access point has received its initial configuration, its LED blinks in a unique pattern to indicate the initial configuration is complete.
Set this value to 1700. The allowed port range is 1 to 65,535.
When a client device requests access to the network, the Cisco ISE RADIUS server presents the client with a URL where a device‘s compliance is checked for definition file validity (this form of file validity checking is called posture). The check verifies, for example, that the device's anti-virus or anti-spyware software is valid. If the device complies, it is allowed access to the network.
Click Reset to revert to the last saved configuration.