A certificate links identity information with a public key enclosed in the certificate.
A CA (certificate authority) is a network authority that issues and manages security credentials and public keys for message encryption. The CA signs all digital certificates it issues with its own private key. The corresponding public key is contained within the certificate and is called a CA certificate. A browser must contain this CA certificate in its Trusted Root Library so it can trust certificates signed by the CA's private key.
Depending on the public key infrastructure, the digital certificate includes the owner's public key, the certificate expiration date, the owner's name and other public key owner information.
Each certificate is digitally signed by a trustpoint. The trustpoint signing the certificate can be a certificate authority, corporation or individual. A trustpoint represents a CA/identity pair containing the identity of the CA, CA-specific configuration parameters, and an association with an enrolled identity certificate.
SSH keys are a pair of cryptographic keys used to authenticate users instead of, or in addition to, a username/password. One key is private and the other is public key. SSH (Secure Shell) public key authentication can be used by a client to access resources, if properly configured. A RSA key pair must be generated on the client. The public portion of the key pair resides with the licensed device, while the private portion remains on the client.
The certificate configuration used by an access point managed device can be changed (overridden) as changes in security credentials require modification in the management of the device.
To override a managed device‘s certificate configuration:
The Device Overrides screen displays. This screen lists devices within the managed network.
The selected access point's configuration menu displays, with the Basic configuration screen selected by default.
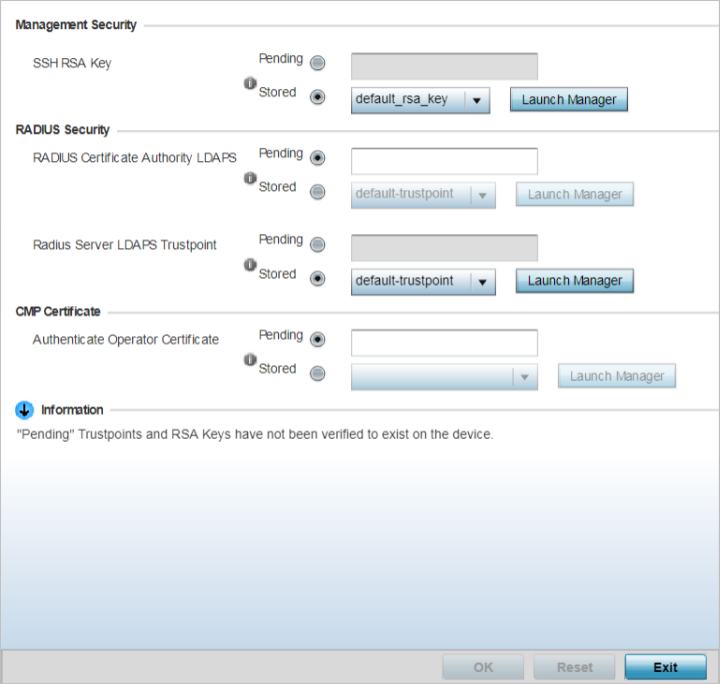
The certificates configuration screen displays.
|
HTTPS Trustpoint |
Either use the default-trustpoint or select the Stored radio button to enable a drop-down menu where an existing certificate/trustpoint can be leveraged. To leverage an existing device certificate for use with this target device, select the Launch Manager button. For more information, see Manage Certificates. |
|
SSH RSA Key |
Either use the default_rsa_key or select the Stored radio button to enable a drop-down menu where an existing certificate can be leveraged. To leverage an existing key, select the Launch Manager button. For more information, see RSA Key Management. |
Pending trustpoints and RSA keys are typically not verified as existing on a device.
|
RADIUS Certificate Authority |
Either use the default-trustpoint or select the Stored radio button to enable a drop-down menu where an existing certificate can be leveraged. To leverage an existing certificate, select the Launch Manager button. |
|
RADIUS Server Certificate |
Either use the default-trustpoint or select the Stored radio button to enable a drop-down menu where an existing certificate/trustpoint can be used. To leverage an existing trustpoint, select the Launch Manager button. |
|
RADIUS Certificate Authority LDAPS |
Either use the LDAP server default-trustpoint or select the Stored radio button to enable a drop-down menu where an existing certificate can be leveraged. To leverage an existing certificate, select the Launch Manager button. |
|
RADIUS Server LDAPS Trustpoints |
Either use the LDAP server default-trustpoint or select the Stored radio button to enable a drop-down menu where an existing certificate/trustpoint can be used. To leverage an existing trustpoint, select the Launch Manager button. |
Use the Launch Manager to view more information on the installed vendor certificates. For more information on managing vendor certificates, seeCrypto CMP Policy.
Selecting Reset reverts the screen to its last saved configuration.