Unknown Devices
The Unknown Devices tab displays a list of all devices on the wired network that were discovered by Extreme AirDefense from the source or destination address in communications from or to a wireless device in your network. If Extreme AirDefense is unable to identify the MAC address listed as the ultimate source or destination, then the identified device is classified as Unknown Device.
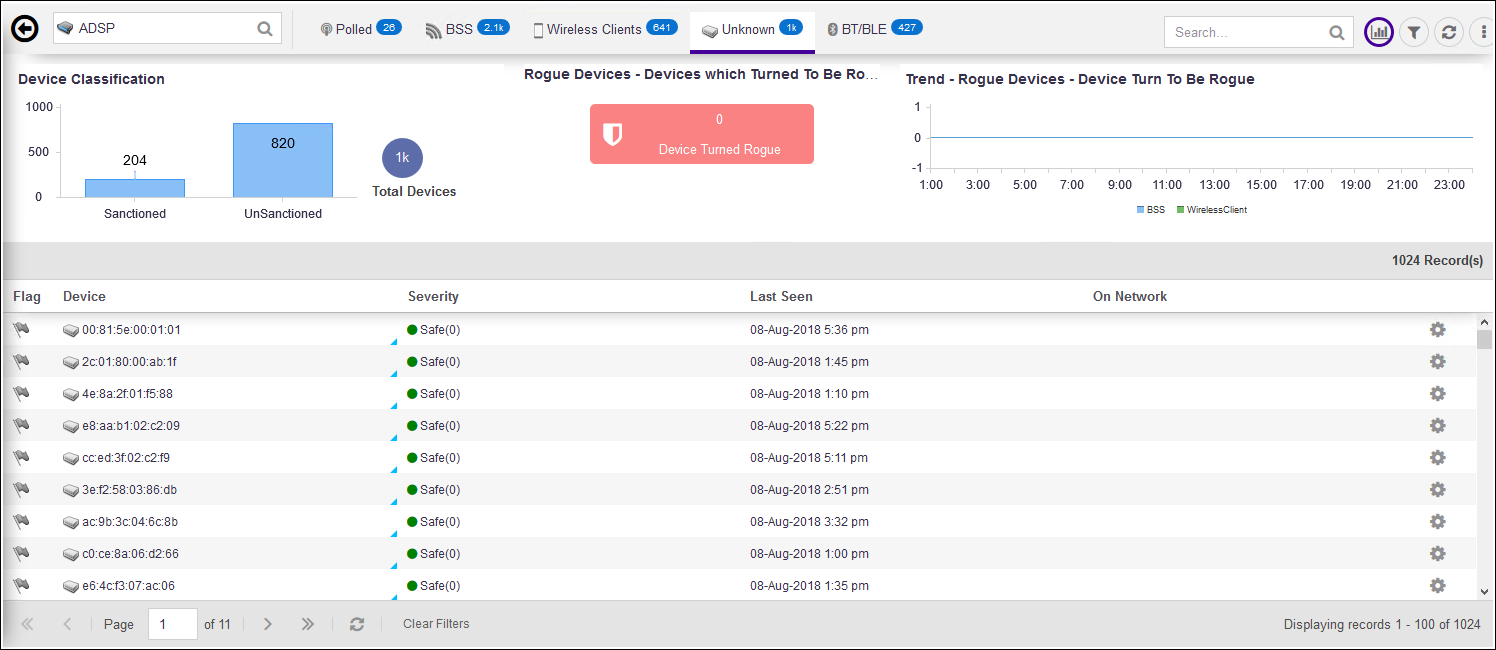
The Unknown Devices table displays the following information:
|
Field |
Description |
|---|---|
|
Flag |
Select the |
|
Device |
This column displays the device type icon and its name. Hover on the name to display more details about the device in a pop-up. The following image is a pop up that displays on hover. 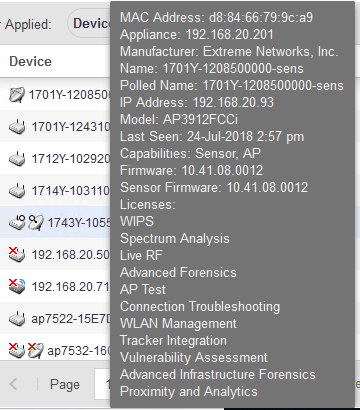 Select the MAC address of the device to view its details in a separate window. |
|
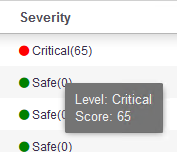
Severity |
This column displays the device's threat level to your network. Hover on this value to display a threat score for this device.
 |
|
Last Seen |
This column displays the date and time this device was last seen on the network. |
|
On Network |
Identifies how ADSP obtained the MAC address of a non-wireless
device. The different entries are:
|
By default, only few columns are displayed in the table. Depending on the context, additional fields can be manually added to the table.
To add/remove table columns,
select the ![]() icon to
the left of any column header. The following drop-down list
displays.
icon to
the left of any column header. The following drop-down list
displays.
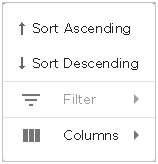
Select the Filter item to filter your data. This option might not be available for all screens. When this option is available, use the available filter criteria to filter the data displayed in the screen.
Select the Columns item to view a list of columns that can be added to the table.
The following table lists the additional columns that can be added to the table.
|
Field |
Description |
|---|---|
|
Name |
This column displays the name of the device if configured. |
|
MAC |
This column displays the MAC address of the device. |
|
IP |
This column displays the IP address assigned to this device. |
|
First Seen |
This column displays the date and time this device was first seen on the network. |
|
Scope |
This column displays the name of the site/location where this device is located as identified by Extreme AirDefense. |
|
Floor |
This column displays the floor number (in the site/location) where this device is located as identified Extreme AirDefense. |
|
Manufacturer |
This column displays the name of the manufacturer of the device. |
|
Classification |
Use this menu item to classify the device into one of Sanctioned (Inherit profiles), Unsanctioned, Neighboring, and Sanctioned (Assigned Profiles). 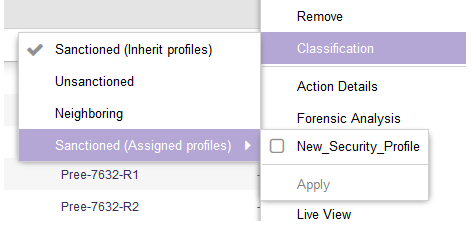 The Sanctioned (Assigned Profiles) menu item expands to show a list of available profiles that can be assigned to this device. |
Device Actions
The following actions can be performed on a each device listed in the table. Select
the ![]() icon to display the list of actions that can be performed. The
actions that can be performed are different for the different device types.
icon to display the list of actions that can be performed. The
actions that can be performed are different for the different device types.
|
Action |
Description |
|---|---|
|
Alarms |
Displays the Alarms for the device. When selected, the alarms for this device are displayed in the Alarms screen |
|
Rename |
Select this menu item to rename this device. Use this menu item to configure a meaningful name for this device. A small window displays. Use this Rename window to provide a name for this device. 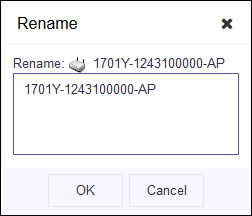 |
|
Remove |
Select this menu item to remove the device. A small confirmation window displays. Select Yes to remove the device. Select No to exit without removing the device. 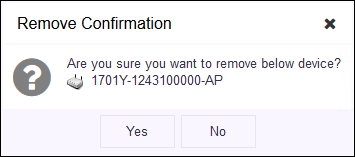 |
|
Classification |
Use this menu item to classify the device into one of Sanctioned (Inherit profiles), Unsanctioned, Neighboring, and Sanctioned (Assigned Profiles). 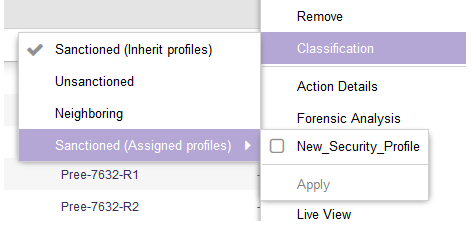 The Sanctioned (Assigned Profiles) menu item expands to show a list of available profiles that can be assigned to this device. |
|
Action Details |
Select the Action Details menu item to view a table listing specific actions occurring on the device. |
|
Add to ACL |
Use this menu item to add this device to the Access Control List. |
|
Forensic Analysis |
Use the Forensic Analysis menu item to analyze the device and provide detailed information on the device. Forensic Analysis returns the threat level of the device, device alarms, and device association details about the device. |
|
Live View |
The Live View menu item displays the Live View window for the device where you can view the device's live status and other parameters. 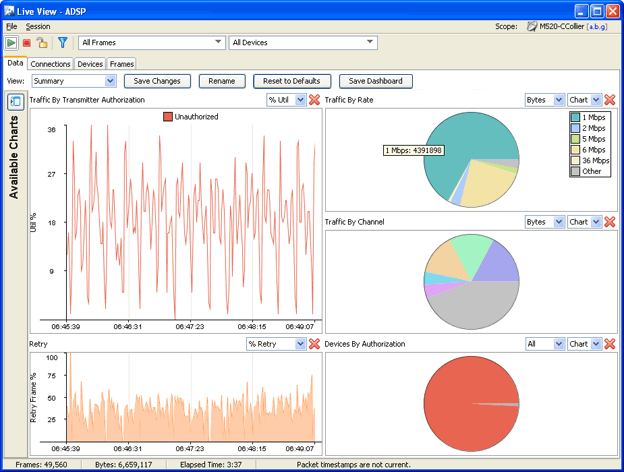 |
|
Port Lookup (Find this Device) |
Use the Port Lookup menu item to scan for and locate this device, in your network, using its MAC address. |
|
Terminate |
Use the Terminate menu item to open the Termination options window from where you can terminate this device. |
|
Copy MAC |
The Copy MAC menu item is an ease of use feature and enables you to copy the MAC address of the device in hexadecimal or colon hexadecimal notation. Click this menu item to expand it and view MAC formats that can be copied. 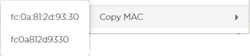 Select the MAC format to copy to your PC's clipboard. |








